Operations | Monitoring | ITSM | DevOps | Cloud
Top Industry Performers in Unplanned Server Downtime | Q1 The Uptime Report
Can you be incompetent and still stay in business? Not as far as your web infrastructure is concerned. All the studies show that when a website is unavailable, or even just slow to load, customers go elsewhere—and often they don’t come back. After all, if you can’t keep a website up and running, why should people trust you to deliver any other product or service? So it’s worth asking: how reliable is your website relative to the top brands in your industry?
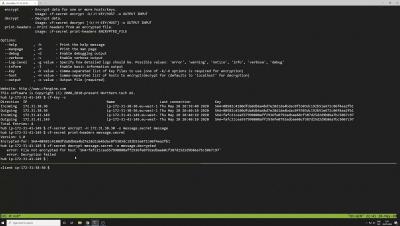
Tools for debugging apps on Google Kubernetes Engine
Editor’s note: This is a follow up to a recent post on how to use Cloud Logging with containerized applications running in Google Kubernetes Engine. In this post, we’ll focus on how DevOps teams can use Cloud Monitoring and Logging to find issues quickly. Running containerized apps on Google Kubernetes Engine (GKE) is a way for a DevOps team to focus on developing apps, rather than on the operational tasks required to run a secure, scalable and highly available Kubernetes cluster.
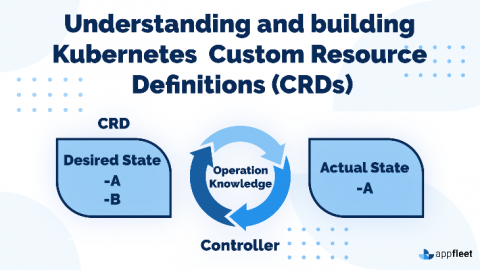
Understanding and building Kubernetes Custom Resource Definitions (CRDs)
So, let's say you had a service or application that was built on an orchestration platform such as Kubernetes. In doing so, you must also address an overflowing array of architectural issues, including security, multi-tenancy, API gateways, CLI, configuration management, and logging. Wouldn't you like to save some manpower and development time and focus on creating something unique to your problem? Well, it just so happens that your solution lies in what's called a Custom Resource Definition, or CRD.
HAProxyConf 2019 - HAProxy Go Packages Ecosystem with Marko Juraga
Introducing Flowmon Packet Investigator
Impact for Everyone! [Twitch]
IT Risk Assessment vs. IT Risk Management: The Difference and What They Mean to the Service Desk
Install Artifactory HA on GKE in a Flash
Installing Artifactory on GKE, or on any Kubernetes cluster for that matter, can be complex. You have to think through several scenarios, switch back and forth between UI and command line, create a lengthy Helm command, search for acceptable parameters … and so on. All this before you have to configure certificates, licenses, database settings, node settings. But there’s more, what about future proofing it?