Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on IT Networks and related technologies.
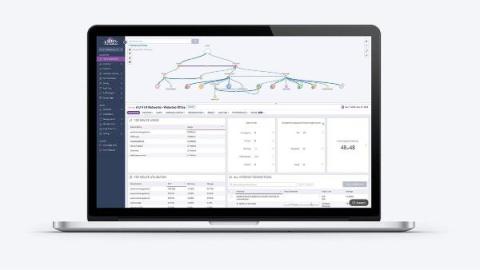
How does observability enhance operations in cloud native voice networks?
The 17th century saw the onset of the Scientific Revolution. It was a time of knowledge explosion. During this time, scientific practices were still evolving, with no universally accepted protocols for data collection and analysis. Individuals documented any observation, resulting in the collection of massive amounts of information, but much of it was hard to leverage to draw useful conclusions. The development of the scientific method provided a common approach to capturing and analyzing data.
Obkio's 2025 Pricing Updates: Investing in a Stronger, Smarter Network Monitoring Solution
For the first time in over 3 and a half years, we’re updating our pricing. Starting June 1st, new pricing will apply to all new purchases, upgrades, and renewals and will be reflected in upcoming billing statements. This change comes as we roll out a wave of powerful new features and improvements designed to help you monitor and optimize network performance better than ever before. We know pricing updates are never taken lightly, and neither is your trust in us.
Cloud Migration Benefits: Why Switching Network Management to the Cloud Makes Sense
Migrating your network infrastructure and management tools to the cloud offers tremendous advantages for modern businesses. As legacy on-premise data centers face growing limitations, shifting critical IT resources into robust cloud platforms provides the agility, efficiency, and innovation needed to stay competitive. This article explores the many benefits of cloud migration, including the financial, operational, and strategic upsides.
Four Ways to Connect Your Clouds
Learn how to connect your cloud environments without sacrificing speed, security, or cost efficiency. Businesses aren’t sticking to just one cloud provider anymore. Maybe you’re running apps on AWS, storing data in Google Cloud, and using Azure for AI workloads. It makes sense – each provider has its own strengths. But now you’ve got another challenge: How do you connect them all efficiently without running into performance issues, high costs, or security risks?
How to find Network Visibility Gaps: Strategies to Ensure Resilience and Performance
As IT infrastructures grow more complex, visibility and resilience have never been more critical. With hybrid IT, remote workforces, and distributed services, your network extends far beyond the data center or cloud—it spans the internet. Traditional monitoring tools leave blind spots that impact user experience and lead to costly downtime. To stay ahead, modern network performance monitoring (NPM) must evolve.
The Scourge of Excessive AS-SETs
An AS-SET is a special object that represents a group of ASNs and forms the basis for IRR-based route filtering. However, many AS-SETs in circulation today have grown so big that they effectively whitelist much of the routing table, rendering them ineffective. According to recent analysis, there are currently 2,192 AS-SETs which expand to over 1,000 ASNs each! In this blog post, we’ll describe what an AS-SET is, its role in route filtering, and how to deal with excessively large AS-SETs.
Auvik's 2025 IT Trends Report is HERE!
Think your network is secure? Spoiler alert: it’s not just cyber threats keeping IT teams up at night. Here's a preview of our 2025 IT Trends Report, which reveals how things like gaps in AI policies & networking tool sprawl are contributing IT pro burnout.
Optimize AWS Transit Gateway Usage
AWS Transit Gateway simplifies network architecture by connecting multiple VPCs and on-premises networks through a centralized hub—but it's easy to incur unnecessary costs if not managed properly. Learn how Kentik provides deep visibility into your AWS Transit Gateway usage, quickly highlighting expensive or inefficient traffic patterns. Using Kentik's Data Explorer, we show how to identify unnecessary intra-VPC traffic that's adding costs and potentially degrading performance.
Top Linode Alternatives for 2025: Why Kamatera Stands Out for DevOps Teams
Businesses continuously explore alternatives to Linode to discover cloud hosting solutions that align perfectly with their diverse needs. Alternative platforms like AWS, Amazon, OVHcloud, and Kamatera offer varied options in terms of pricing, features, and performance capabilities. Shifting to these alternatives might provide better integration options, improved customer support, or pricing benefits suited for different business scales. This exploration enables organizations to secure a cloud platform that meets their specific requirements and supports their growth trajectory effectively.