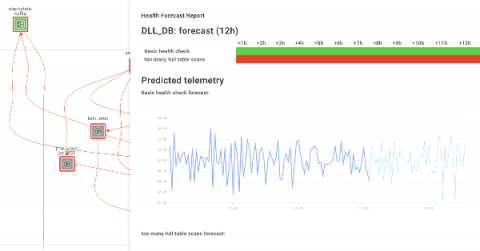
The Cost of Doing SIEM & Security Analytics on Your Own
Security information and event management, or SIEM, has become part of the vocabulary of every organization. SIEM solutions gather events from multiple systems and analyze them—both in real time and through historical data. SIEM costs—as cyber security costs in general—can be high, but there is a tradeoff if you opt for the FOSS route (free and open source solutions).