Operations | Monitoring | ITSM | DevOps | Cloud
How to Explain Zero Trust to Your Tech Leadership: Gartner Report
Does it seem like everyone’s talking about Zero Trust? Maybe you know everything there is to know about Zero Trust, especially Zero Trust for container security. But if your Zero Trust initiatives are being met with brick walls or blank stares, maybe you need some help from Gartner®. And they’ve got just the thing to help you explain the value of Zero Trust to your leadership; It’s called Quick Answer: How to Explain Zero Trust to Technology Executives.
Zero Trust: The New Security Model for Cloud Native Applications and Infrastructure
Zero Trust security is gaining attention and momentum as a security approach or mindset that can improve the security posture of enterprises as they continue to battle hackers. Because of this widespread attention on Zero Trust, every software security vendor seems to be jumping on the Zero Trust bandwagon. However, Zero Trust is not a product or service. No single product or vendor can sell you Zero Trust security.
Zero Trust is NOT enough...
The current trend to move to Zero Trust security architectures using the mantra “Never Trust, Always Verify” is a move that Teneo has long supported. The simple fact is that the traditional castle and moat approach to security built on VPNs is not fit for purpose in the modern world with hybrid users and infrastructures.
Making Sure the Future of Federal Work Is Secure and Enjoyable - Why We're Partnering with NIST on Its Zero Trust Project
Last year, we announced our partnership with the National Cybersecurity Center of Excellence (NCCoE) at the National Institute of Standards and Technology (NIST) to work on the Implementing a Zero Trust Architecture project. After a year of collaboration with its industry partners, including Ivanti, NIST recently released its preliminary draft, NIST Cybersecurity Practice Guide SP 1800-35 Vol B, for public comment.
Zero Trust Security: Key Concepts and 7 Critical Best Practices
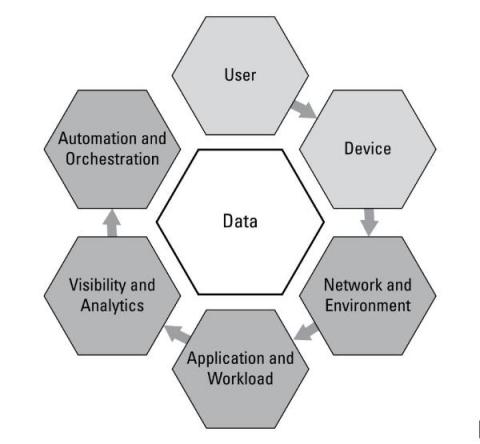
Zero trust is a security model to help secure IT systems and environments. The core principle of this model is to never trust and always verify. It means never trusting devices by default, even those connected to a managed network or previously verified devices. Modern enterprise environments include networks consisting of numerous interconnected segments, services, and infrastructure, with connections to and from remote cloud environments, mobile devices, and Internet of Things (IoT) devices.
What is Zero-Trust? How can it be a game-changer for the security, control, and monitoring of your IT infrastructure?
Using Zero Trust Networking in Cloud Migrations
Moving workloads to the cloud has many benefits, and one that is often overlooked is the opportunity to modernize your network. In a traditional “perimeter-based” architecture, users and devices are authenticated and authorized on a device-by-device basis when connecting remotely via VPN.
Puppet and Government: Achieving Zero Trust adoption and mission success at the same time
Government agencies have been working diligently to comply with the 2021 Executive Order on Improving the Nation’s Cybersecurity. The Executive Order (EO) addresses cybersecurity issues by imposing a new series of federal-wide Zero Trust mandates. Agencies were required to submit their plan development and cloud migration path reporting by July and August of 2021, with more deadlines on the horizon.