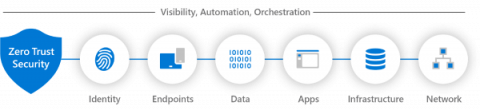
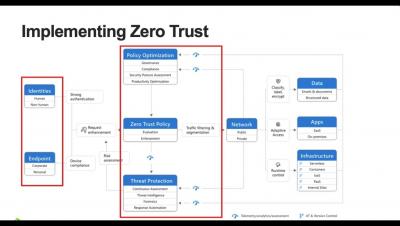
Understanding Zero Trust Principles
Have you ever wondered how to keep your digital assets truly secure in a world where cyber threats seem to evolve quicker than cybersecurity measures? If so, you might want to consider adopting a Zero Trust security model. Far from being a buzzword, Zero Trust has emerged as a holistic approach to cybersecurity that operates on a straightforward principle: “Never Trust, Always Verify”.