Operations | Monitoring | ITSM | DevOps | Cloud
What is Zero Trust and How IT Infrastructure Monitoring (ITIM) Makes it Happen
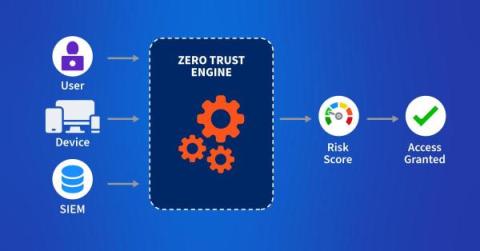
When the concept of Zero Trust emerged in 2010, it marked a sea change in how IT and network security are handled. The term, invented by Forrester Research analyst John Kindervag, is loosely based on the “never trust, always verify” motto. So why is this a sea change? Before 2010, IT focused on perimeter defenses and the concept of DMZs — areas of the network they deemed safe based on the protection they implemented.
What is Zero Trust and How IT Infrastructure Monitoring (ITIM) Makes it Happen
When the concept of Zero Trust emerged in 2010, it marked a sea change in how IT and network security are handled. The term, invented by Forrester Research analyst John Kindervag, is loosely based on the “never trust, always verify” motto. So why is this a sea change? Before 2010, IT focused on perimeter defenses and the concept of DMZs — areas of the network they deemed safe based on the protection they implemented.
Security Webinar: Navigating the Zero Trust Journey for Today's Everywhere Workplace
Adopting a Zero-Trust Strategy
Zero-Trust Security: Best Practices for Securing the Remote Workforce
Security Webinar, Zero Trust For Users
How to Harden Zero-Trust Cloud Network Policy with Kentik
Zero trust in the cloud is no longer a luxury in the modern digital age but an absolute necessity. Learn how Kentik secures cloud workloads with actionable views of inbound, outbound, and denied traffic.
Zero Trust - An Analyst's 10-Minute Perspective
The Landscape of Zero Trust Adoption: Insights from Our 2023 Zero Trust Progress Report
Organizations are responding to the changing cybersecurity landscape. And zero trust is at the heart of this change, with 68% of respondents saying they’re planning or actively working towards adopting a zero trust access model. In collaboration with Cybersecurity Insiders, Ivanti surveyed 421 US-based IT and cybersecurity professionals to identify the latest enterprise adoption trends, challenges, gaps and solution preferences related to zero trust security.