Operations | Monitoring | ITSM | DevOps | Cloud
Elasticsearch security: Authentication, Encryption, Backup
There’s no need to look outside the Elastic Stack for apps to ensure data protection. Basic Elasticsearch Security features are free and include a lot of functionality to help you prevent unauthorized access, preserve data integrity by encrypting communication between nodes, and maintain an audit trail on who did what to your stack and with the data it stores. From authentication to encryption and backup, Elasticsearch security covers everything that’s needed to safeguard your cluster.
AlertBot Tutorial: Schedule an Email Report
AlertBot Tutorial: Setting up a Do Not Disturb Schedule
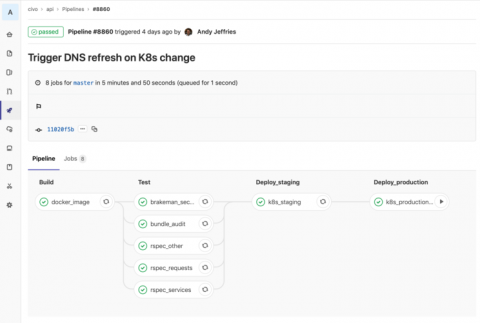
CI/CD/Civo/C-what?
As a cloud provider and DevOps-focused company, we definitely want to practice what we preach. We see the benefits of a modern cloud native architecture, so we built our hosting of www.civo.com and api.civo.com (our application) to take full use of these modern decisions. This post describes our approach to Continuous Integration (CI) and Continuous Deployment (CD) from a Chief Technical Officer's perspective.
Icinga Cube 1.1.0 is out!
As a little introduction for everyone who has not heard about the cube yet: The cube module is there to show statistics grouped by the custom variables that have been set for the hosts and services. They are then displayed in up to three dimensions for a quick overview to show the relations. The most prominent change is the addition of services: While it used to be only possible to have the hosts in a cube, the module has now been extended to provide full functionality with services as well.
The other half of software: what lurks between business logic
In 2016 I was the tech lead for a greenfield project completely devoid of legacy–I held the engineer’s promised land in front of me! I bit off as much new stuff as I could – serverless, event sourcing, functional programming, the whole gambit of cool. This is normally a very bad idea, but I had a team of strong engineers who had prior experience in this stuff, and we were ready to be technology pilots for the broader organization.
How No-Code Integrations Help Incident Management Scale
Do you think no-code is just another buzzword that with no real meaning? Well, maybe it is in some contexts. But if you want an example of how no-code solutions can matter in the real world, look no further than the context of incident management. Let us explain by walking through what no-code solutions mean in the context of incident management, how they work and how they can help teams scale and streamline their operations.
2019 Hurricane Season: Solidify a Business Continuity Plan With a Mass Notification Solution
Summer is typically synonymous with beach days, outdoor barbecues and fulfilling weekend getaways. Unfortunately, the summer months aren’t only about enjoyable moments and exciting vacations. It’s also tropical storm season, with higher risks of destruction, community displacement and business operation disruption. With this potential for human and business peril, it’s important for organizations to implement a business continuity plan, equipped with a robust communication strategy.
3X Growth is Quite a Milestone, And It's Only the Beginning
When you start a company – or a third company as is the case for Lee and me – you start with a problem statement, a product you believe in, and a lot of hope. This means when growth goes as planned or exceeds expectations, you shouldn’t be surprised. This is what is supposed to happen. Great Product + Market Opportunity + Great Team = Successful Business. Intellectually, I know all this, but it is still exciting to see it come to fruition.