Operations | Monitoring | ITSM | DevOps | Cloud
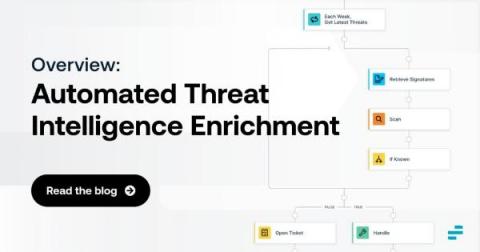
Automated Threat Intelligence Enrichment: An Overview
Discovering security threats is good and well. But, in many cases, simply knowing that a threat may exist is not enough. Instead, you also need threat intelligence enrichment. Threat enrichment plays a critical role in helping to evaluate and contextualize threats, root out false positives and gain the insights necessary to mitigate risks as efficiently and quickly as possible.
Processes, forks and executions - part 1
While working on the integration of CFEngine Build into Mission Portal we came to the point where we needed to start executing separate tools from our recently added daemon - cf-reactor. Although it may seem like nothing special, knowing a bit about the process creation and program execution specifics (and having to fight some really hard to solve bugs in the past) we spent a lot of time and effort on this step.
Stop putting off patching!
Let's face it: no one likes patching. When I was a practitioner, we always put off patching until it was absolutely necessary. Until a business need – such as updating an application version or support ending for a version – arose, we didn't patch because "If it ain't broke, don't fix it." We all know this is a bad practice; let's remind ourselves why. The longer a system goes without being patched, the more changes will accumulate.
The Future is Smart Cloud-Native
The future of cloud automation for SAP with AWS and Avantra
Azure Automation Best Practices
Kelverion have put together this Azure Automation Best Practices Guide to support the creation of automation process in Azure Automation. Our consultants work with Azure Automation every day and have substantial experience with Azure Automation and IT automation built using other tools. It’s important to recognize that these are recommendations rather than hard and fast rules.
Automate Your Boring Tasks with Ruby
If you aren’t already fed up with doing the same boring stuff over and over again, you will In the long run. Tasks which are repeated again and again in the same manner, such as System administration tasks, such as uploading your codebase, adjusting settings, repeatedly running commands, etc. tend to sap the enthusiasm you experience when working on your project.
IDC report: How autonomous compliance ensures better business outcomes
A new report from IDC emphasizes just how critical autonomous compliance is for companies to ensure that their digital infrastructure environments are consistently hardened, resilient, and compliant. Leaders who prioritize compliance optimize company efficiency while reducing risk. The IDC PeerScape report outlines the best practices of these leaders, who, by implementing autonomous compliance, better protect their businesses.