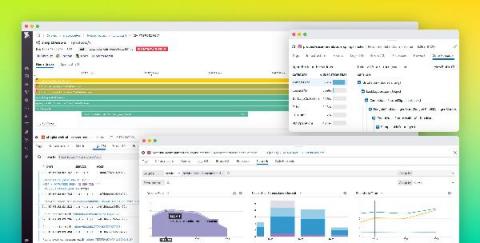
Where is Your Next Release Bottleneck?
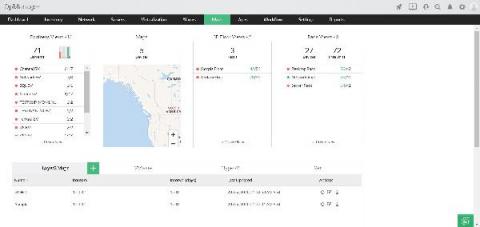
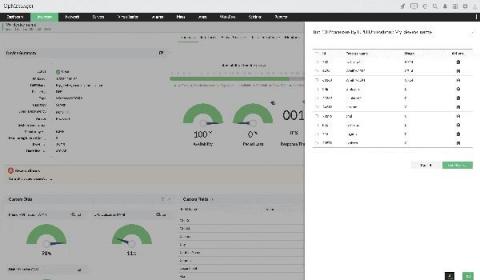
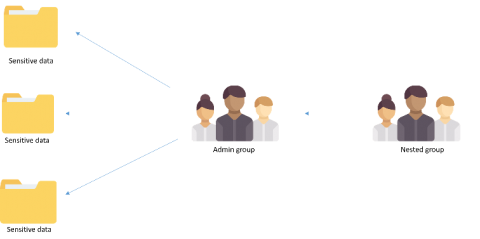
A typical modern DevOps pipeline includes eight major stages, and unfortunately, a release bottleneck can appear at any point: These may slow down productivity and limit a company’s ability to progress. This could damage their reputation, especially if a bug fix needs to be immediately deployed into production. This article will cover three key ways using data gathered from your DevOps pipeline can help you find and alleviate bottlenecks in your DevOps pipeline.