Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
Fresh Springtime Product Updates: D2iQ Kommander 1.4 and D2iQ Konvoy 1.8 Are GA!
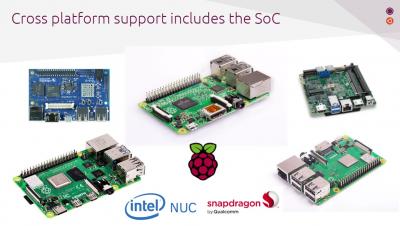
It’s that time again: the latest versions of D2iQ Konvoy and D2iQ Kommander have just been made generally available and the D2iQ Kubernetes Platform (DKP) has some powerful new features. As noted with our last update, DKP is the leading independent Kubernetes platform for enterprise grade production at scale and Konvoy and Kommander are the reason why. You can learn more about Konvoy here, Kommander here, and our general approach here.
Announcing HAProxy Kubernetes Ingress Controller 1.6
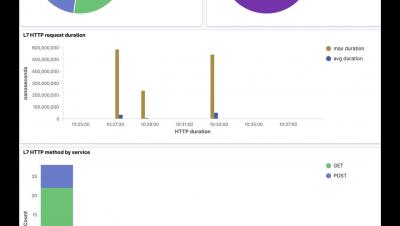
Application Layer Observability | Tigera - Long
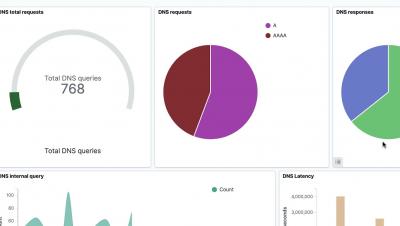
DNS Dashboard | Tigera - Long
Kubernetes: Weighing Advantages and Disadvantages
Kubernetes is one of the current leading technologies. Its adoption has seen tremendous growth in the past few years. The concept of containers is a paradigm that appears to be the predominant medium of software development and deployment in the coming future. Containers help maintain consistency across various platforms, as they pack an application with its dependencies to help move it from one platform to another.
Launching Argo CD Autopilot: An Opinionated Way to Manage Your Applications Across Environments Using Gitops at Scale
Argo CD has been skyrocketing in popularity with the CNCF China survey naming Argo as a top CI/CD tool for its power as a deployment automation tool. And it’s no wonder, GitOps is a faster, safer, and more scalable way to do continuous delivery. Most of our own users are embracing GitOps to manage infrastructure and applications at scale in gaming, finance, defense, media, and other industries.
Calico Enterprise enables live view of cloud-native apps deployed in Kubernetes
We are happy to announce that the latest release of Calico Enterprise delivers unprecedented levels of Kubernetes observability! Calico Enterprise 3.5 provides full-stack observability across the entire Kubernetes environment, from application layer to networking layer. With this new release, developers, DevOps, SREs, and platform owners get: For more information, see our official press release.
Civo official launch!
Securing AWS Fargate workloads: Meeting File Integrity Monitoring (FIM) requirements
Securing AWS Fargate serverless workloads can be tricky as AWS does not provide much detail about the internal workings. After all… it’s not your business, AWS manages the scaling of underlying resources for you. :) While the security and stability of Fargate’s system is an inherent feature, Fargate follows a shared responsibility model, where you still have to take care of securing those parts specific to your application..