Operations | Monitoring | ITSM | DevOps | Cloud
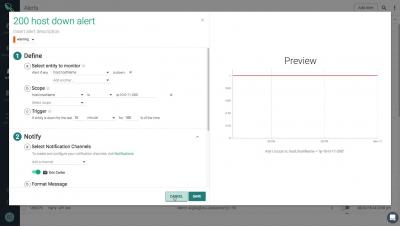
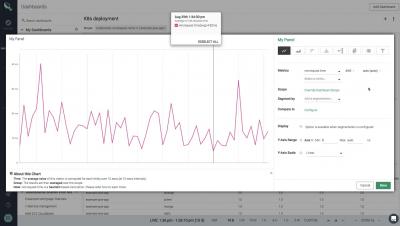
Sysdig Monitor Dashboards
IBM Cloud Monitoring with Sysdig Monitor
The role of SIEM in PCI DSS compliance
Studies have shown a direct correlation between data breaches and non-compliance. This isn’t to say that compliant companies never get breached, but to reinforce the importance of incident detection and response. Businesses have begun to realize the devastating consequences of data breaches—their finances and reputation are at stake, so many have been taking steps over the last few years to comply with the PCI DSS. The main goal is often an emphasis on achieving continuous compliance.
We've launched an Azure Meetup!
Azure lovers, we have good news for you. Our new years resolution in 2019 is to support the local Azure community. We kicked off with our first Azure Meetup in December. And as the numbers below suggest... people had a great time.
Adding CVE scanning to a CI/CD pipeline
A Docker image contains an application and all its dependencies. As it also contains the numerous binaries and libraries of an OS, it’s important to make sure no vulnerabilities exist in its root filesystem, or at least no critical or major ones. Scanning an image within a CI/CD pipeline can ensure this additional level of security.
Increased Visibility to Manage the New Java Release & Support Model
According to Oracle, Java is a fast, secure and reliable programming language and computing platform first released by Sun Microsystems in 1995. There are lots of applications and websites that will not work unless Java is installed, and more are created every day. From laptops to datacenters, game consoles to scientific supercomputers, cell phones to the Internet, Java is everywhere.
Top 5 DevOps Tools to use before deploying your code
DevOps is an ongoing process requiring constant communication, collaboration, and automation. Teams must be able to move projects from conceptualization to release as quickly and as efficiently as possible. Not only do organizations need to have workflows in place to facilitate DevOps, but they also need the right tools.