Auvik Named a Leader Across G2's Winter 2026 Reports for Network Management
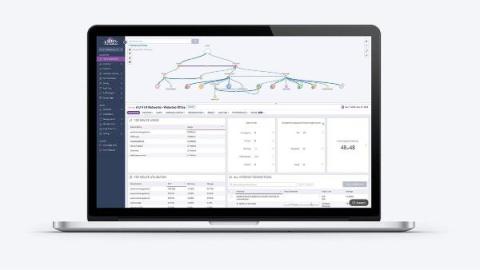
In G2’s Winter 2026 reports, Auvik earned top recognition as a leader in network management tools across small-business, mid-market, and enterprise categories. IT professionals rated Auvik highly for implementation, usability, results, relationship, and overall Grid® performance, reflecting one thing above all: real-world trust from the IT professionals who use Auvik every day.