Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
Single Sign-On for Kubernetes: Dashboard Experience
Over my last two posts (part 1 and part 2), I have investigated user authentication in Kubernetes and how to create a single sign-on experience within the Kubernetes ecosystem. So far I have explained how Open ID Connect (OIDC) works, how to get started with OIDC and how to perform a login from the command line. The final piece of this puzzle is the Kubernetes dashboard, often used by our engineers alongside kubectl.
3 Layers to Defend Your Kubernetes Workloads
Researchers at Netflix and Google recently reported a vulnerability in the HTTP/2 protocol that enables adversaries to execute a DOS attack by legitimate use of the protocol. These types of attacks are very difficult to detect and mitigate because the traffic is valid HTTP/2 traffic. While HTTP/2 is a relatively new protocol it should be noted that even after several years of hardening we still see vulnerabilities for the TCP protocol like the recently reported SACK vulnerability.
Startup CTO: How to Onboard a New Software
Once you’ve hired a software engineer, it’s easy to feel like the recruiting process is over. However, the first few days and weeks of your new engineer’s experience are critical to their long term success and happiness at your startup. In this last part of our series on hiring software engineers as the CTO of a startup, we’ll talk about how we onboard software engineers at Blue Matador and the insights I’ve gained in this part of the CTO experience.
Calling Codefresh pipelines from Github actions
At Codefresh we are all about collaboration and reusing existing standards instead of implementing proprietary solutions. A Codefresh pipeline is based on a series of Docker containers that act as individual steps. All Codefresh plugins are also just Docker images which means that extending a Codefresh pipeline is the same thing as writing a Dockerfile. Github has recently announced an integrated automation solution called Actions.
Rancher and Arm Partner to Accelerate Edge Computing
Edge computing has become a clear strategic goal for many enterprises, for some it is already an absolute necessity. As the demands of applications software and the capabilities of hardware continue to grow, containers and Kubernetes have become a compelling technology for edge computing. In just the past 5 years, the way that software is manufactured and maintained has changed dramatically with the introduction of Kubernetes container orchestration.
Kubernetes Phase 2-Key Challenges at Scale
Kubernetes is THE buzzword these days. Almost every IT organization is currently using it or is in the process of implementing it as part of their infrastructure. The transition to Kubernetes is complicated, whether a company is using an on-premises, cloud, hybrid, or managed solution, and it usually involves other changes in the codebase, such as shifting to a microservices architecture. While the implementation phase is led by the DevOps team, it requires the participation of the whole R&D group.
September 2019 Online Meetup: Implementing Infrastructure as Code
How to Secure a Kubernetes Cluster
Kubernetes is one of the most advanced orchestration tools that currently exists in the software world. It provides out-of-the-box automation for environment maintenance and simplifies deployment and upgrade processes. It has different implementation types (on-premise, cloud-managed, hybrid, and more), multiple open-source supporting tools, and supports a wide range of configuration options.
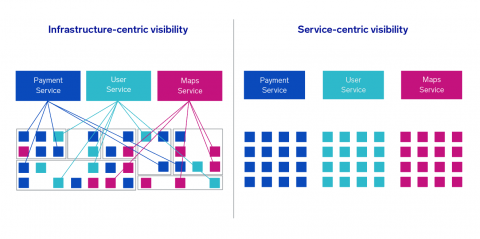
Why Traditional Kubernetes Monitoring Solutions Fail
Kubernetes has several key differences that push the limits of traditional application monitoring. Due to the distributed ephemeral nature of Kubernetes, most existing solutions fail to give the visibility we might expect, resulting in longer resolution times. Looking at these potential pitfalls can help guide us as we take a fresh look at Kubernetes management and monitoring.