Operations | Monitoring | ITSM | DevOps | Cloud
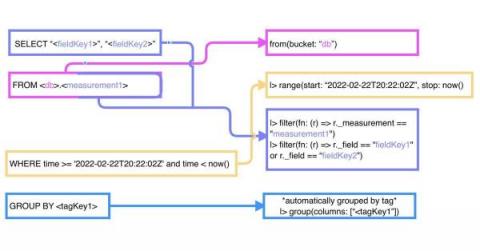
TL;DR InfluxDB Tech Tips: Converting InfluxQL Queries to Flux Queries
If you’re a 1.x user of InfluxDB, you’re most likely more familiar with InfluxQL than you are with Flux. To gain a deep understanding of Flux, it’s important to understand: However, you can still use Flux without studying those topics. In this TL;DR, we’ll convert common InfluxQL queries into Flux and identify patterns between the two languages to help you get started using Flux more easily if you come from a InfluxQL or SQL background.
Building Your Security Analytics Use Cases
It’s time again for another meeting with senior leadership. You know that they will ask you the hard questions, like “how do you know that your detection and response times are ‘good enough’?” You think you’re doing a good job securing the organization. You haven’t had a security incident yet. At the same time, you also know that you have no way to prove your approach to security is working. You’re reading your threat intelligence feeds.
Spark Performance Monitoring using Graphite and Grafana
In this article, we will explore what Apache Spark is, what key metrics you need to track to keep it running, and how to set up a metrics tracking process. We will also cover monitoring tools such as Graphite and Grafana, which make the process of monitoring metrics very easy, as well as how using MetricFire can make running your monitoring exponentially easier. Check out MetricFire for free or book a demo with our team and learn more about all the benefits of using MetricFire solutions.
IoT Made Easy with Node-RED and InfluxDB
In this article you will learn about Node-RED, a popular tool for rapidly gluing together different types of hardware and software. You’ll learn about some of the core concepts of Node-RED and then learn how to make some workflows like storing data from a sensor using an MQTT broker and InfluxDB.
Data-Driven Enterprise (or Just Talking Like One)?
Who’s faking it? Data-driven decision-making (and ensuring related investment is delivering on its promises) has been elevated in importance. Every enterprise is replacing opinion with data-driven decision-making, correct? A brand new research report from EMA (Enterprise Management Associates) titled, “A Data-Driven Enterprise” looks behind the curtain to separate facts and reality from fiction and aspiration. Here are some of the findings from the latest research on enterprises.
Service item reporting made easy using Freshservice
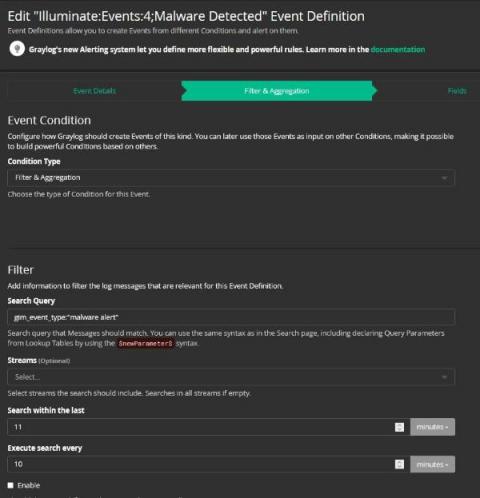
Cybersecurity Risk Management: Introduction to Security Analytics
It’s mid-morning. You’re scanning the daily news while enjoying a coffee break. You come across yet another headline broadcasting a supply chain data breach. Your heart skips a quick, almost undetectable, beat. You have the technology in the headline in your stack. You set aside your coffee and begin furiously scanning through the overwhelming number of alerts triggered across all your technologies.
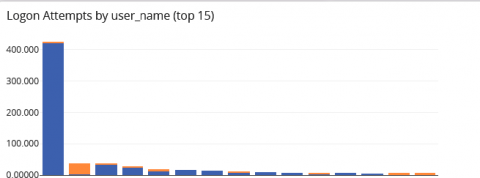
Reporting Up: Recommendations for Log Analysis
What kind of log information should be reported up the chain? At a certain point during log examination analysts start to ask, “What information is important enough to share with my supervisor?” This post covers useful categories of information to monitor and report that indicate potential security issues. And remember: reporting up doesn’t mean going directly to senior management. Most issues can be reported directly to an immediate supervisor.
InfluxData Recognized for Industry Leadership in 2022 Data Breakthrough Awards
InfluxDB wins Best Use of Data for IoT Applications category SAN FRANCISCO, March 29, 2022 – InfluxData, creator of the leading time series platform InfluxDB, today announced InfluxDB has been named a winner in the Data Breakthrough Awards for the Best Use of Data for IoT Applications category. Conducted by Data Breakthrough, an independent market intelligence organization, the awards recognize the top companies, technologies and products in the global data technology market today.