Operations | Monitoring | ITSM | DevOps | Cloud
AMP vs. PWA - All You Should Know
The world of mobile phones is growing at a higher pace by changing the face of digital publishing. Such a rapid change is figured out from Google as it has led to the development of new handful technology which is designed for delivering faster and richer mobile experiences to the users. This is related to the Accelerated Mobile Pages (AMP) by Google and Progressive Web Application (PWA).
Useful tools to manage your application's secrets
When you build and deploy an application, chances are that you need to store some form of secrets. These are typically things like credentials for 3rd party systems and database credentials. As an ASP.NET Core developer, Microsoft provides you with an easy way to store secrets like these in your development environment, namely the Secret Manager.
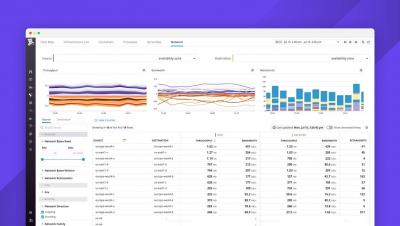
Monitor JavaScript console logs and user activity with Datadog
Monitoring backend issues is critical for ensuring that requests are handled in a timely manner, and validating that your services are accessible to users. But if you’re not tracking client-side errors and events to get visibility into the frontend, you won’t have any idea how often these issues prompt users to refresh the page—or worse, abandon your website altogether.