Operations | Monitoring | ITSM | DevOps | Cloud
New feature alert: OpManager MSP's NCM add-on for a seamless configuration and compliance management
According to ABC News, there has been a 600% rise in security intrusions during the COVID-19 pandemic, which is expected to double before 2025. In many circumstances, admins and technicians either intentionally or unintentionally play a part in the process of derailing the organization’s strategy for success. In order to prevent such mishaps, MSPs need a recovery plan to recuperate from any unfortunate accidents or cyberattacks.
Traceroute software-the troubleshooting tool your network needs
The need for in-depth network monitoring is growing exponentially as organizations expand in size and more companies are established. Increased monitoring needs demand a feature-rich tool to simplify networks and get a clear view of their underlying infrastructure. Diagnosing network faults and ensuring a well-balanced operation of all network devices is the primary task of a network admin any day.
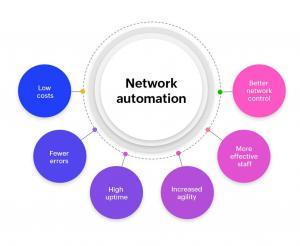
Network automation tools
“Automation applied to an inefficient operation will magnify the inefficiency.” – Bill Gates A network, as we all know, is the connection of multiple devices to share information between them. While it’s a major task to manually manage every device connected to a network, a software-based feature called network automation can be utilized to help overcome this challenge.
Introducing space management for the facilities service desk instance
Introduction to Fail Over Service (FOS)
6 ways your organization can benefit from a network management solution
In today’s world, businesses depend on the internet and networks for nearly all their operations. Most large-scale corporations from banks to IT services have their critical operations built around a network. With network types ranging from wired and wireless to virtual environments, network management has only become increasingly complex, and network administrators need all the help they can get.
Get the most out of your Hyper-V infrastructure using ManageEngine OpManager
Virtualization is the technique of creating a software-based virtual version of something, whether that be computers, storage, networking, servers, or applications. Virtualization creates a virtual layer over the hardware, enabling the creation of virtual machines (VMs), which are virtual computers that you can run multiple of on a single piece of hardware.
Know your network needs: A simple guide to why you need a bandwidth monitoring tool
Understanding the needs of your network is vital to keep your network up and running. In the wake of the remote work era, it’s important to monitor and plan your bandwidth utilization. Recent surveys have reported a 45% increase in VoIP and video traffic as the need for telecommuting has doubled since the pandemic. Business Wire, a broadband provider, also reported a 30% spike in data traffic and a 50% rise in voice traffic since mid-March.
The whats, whys, and hows of Windows network monitoring
Microsoft Windows is one of the most widely used operating systems and is preferred by users all around the world. A Windows device is associated with a lot of processes, services, and events that often need to be tracked from a single console. This is where a Windows network monitoring tool comes in handy. A Windows network monitoring tool is used to monitor the availability and performance of Windows devices in a network.