Operations | Monitoring | ITSM | DevOps | Cloud
From plan to practice to prevail: my conversation with Chris Johnson, host of the MSSP 1337 podcast
The 6th DORA requirement no one told you about
Gett replaces paging tool with Exigence to achieve IR excellence
Why robust IR planning is critical for NIS2 compliance
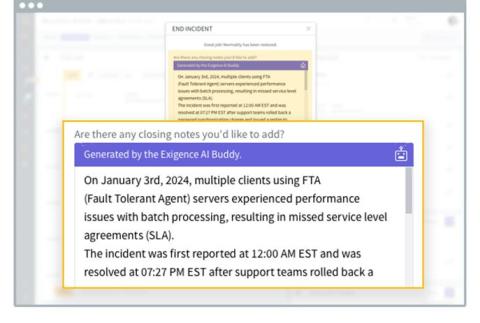
New! incident summary automation with generative AI
How MSPs and MSSPs can reduce risk and liability for their clients
For 83% of companies, a cyber incident is just a matter of time (IBM). And when it does happen, it will cost the organization millions, coming in at a global average of $4.35 million per breach. Add to that stringent data protection laws and the growing frequency and reach of ransomware and other sophisticated attacks.
Automate insights-rich incident summaries with generative AI
Does this sound familiar? The incident has just been resolved and management is putting on a lot of pressure. They want to understand what happened and why. Now. They want to make sure customers and internal stakeholders get updated about what happened and how it was resolved. ASAP. But putting together all the needed information about the why, how, when, and who, can take weeks. Still, people are calling and writing. Nonstop.
How generative AI is increasing cyber risk & what to do to make sure you're ready
Generative AI is all the buzz these days with the popularity of platforms and tools such as ChatGPT, Bard, Scribe, Jasper, and others experiencing exponential growth. This is a technology that has come to the fore with the force of a runaway train that’s bringing us head long into the future at the speed of light. It is transforming everything we do from writing code to making travel plans. And cybersecurity is no exception.
How summertime turns up the heat on cyber readiness (and what to do about it)
“Malicious cyber actors aren’t making the same holiday plans as you.” (CISA & FBI) Summertime is prime time for cyberattacks. According to one survey, 58% of security professionals believe that there is seasonality in the attacks that their company experiences every year, with the majority citing summer as high season for breaches.