Operations | Monitoring | ITSM | DevOps | Cloud
Why Cross-Domain Topology Seems Too Good To Be True
There are some things in life that seem too good to be true. So good, in fact, that they border on the edge of mythology. We see this often in the case of Cross-Domain Topology. Cross-Domain Topology ties together all the pieces of a hybrid, dynamic IT environment, so you can instantly see how changes impact your environment. It’s something that a lot of people didn’t even think was a possibility. While unicorns are myths, Cross-Domain Topology is very real. Here’s how it works.
Extending the Zero-Trust Security Framework to Your Home
Mixing your personal and work devices while connected to your home network and accessing the Internet is a risky proposition from a security and privacy standpoint. Why? I frequently monitor my firewall logs. What I observe on my WAN interface are blocked IP addresses sourced from adversarial nation states which makes the hair on the back of my neck stand up.
Icinga 2 Config Language (DSL): Advanced Apply Rules
As many users of Icinga don’t know what the DSL has to offer, I’m going to show you how to use custom variables and apply for rules to make your life easier when writing configuration for your Icinga environment. In this example we will use custom variables on a host to configure a dynamic set of services to monitor multiple web services behind a reverse proxy. On the host we define a custom dictionary called http_vhosts and assign our virtual hosts to it.
Why Your Website Host's "100% Guaranteed Uptime" Promise is Bogus - and What to Do About It
It’s been said that the devil is in the details. Well, along the same lines — and as we all know from miserable experience — when it comes to guarantees, the devil is in the small print. And there’s no better (or worse) example of this than with respect to the gleaming, confidence-inspiring claim by web hosts that they deliver 100% guaranteed uptime. Except, well, they don’t.
Debugging with Dashbird: Malformed Lambda Proxy Response
One problem that pops up quite frequently when people try to build serverless applications with AWS API Gateway and AWS Lambda is Execution failed due to configuration error: Malformed Lambda proxy response. There is nothing worse than generic error messages that don’t tell you anything you need to fix the problem, right? And AWS isn’t particularly known for its error message design, if you can even call it that, let alone for giving you the means of fixing the problem.
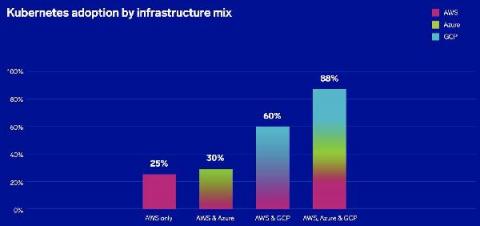
Faster and safer application deployments on Kubernetes with Shipa and Oracle Kubernetes Engine (OKE)
Shipa’s application management framework, integrated into OKE, provides an out-of-the-box way for organizations to build, deploy and operate the full life-cycle of Kubernetes applications. With Shipa and OKE, organizations can make up for lost time and start getting value out of Kubernetes immediately. In this webcast, you will learn how Shipa and OKE.
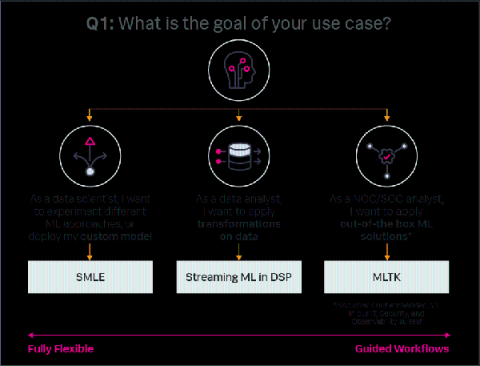
Machine Learning Guide: Choosing the Right Workflow
Machine learning (ML) and analytics make data actionable. Without it, data remains an untapped resource until a person (or an intelligent algorithm) analyzes that data to find insights relevant to addressing a business problem. For example, amidst a network outage crisis a historical database of network log records is useless without analysis. Resolving the issue requires an analyst to search the database, apply application logic, and manually identify the triggering series of events.