Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
2 ways to set up static IP addresses for ALB
One highly requested feature of AWS’s Application Load Balancer is the ability to assign static IP addresses. Unfortunately, ALBs do not support this feature and it is unlikely they will in the near future. Today, the only way to achieve static IP addresses for your application behind an ALB is to add another layer in between the client and your ALB which does have a static IP address, and then forward requests to your ALB.
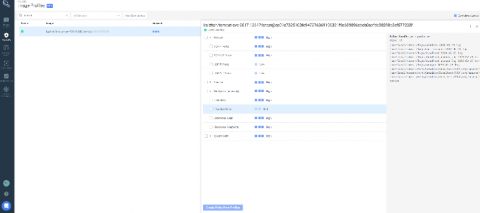
Manage AppArmor profiles in Kubernetes with kube-apparmor-manager
Discover how Kube-apparmor-manager can help you manage AppArmor profiles on Kubernetes to reduce the attack surface of your cluster. AppArmor is a Linux kernel security module that supplements the standard Linux user and group-based permissions to confine programs to a limited set of resources. AppArmor can be configured for any application to reduce its potential attack surface and provide greater in-depth defense.
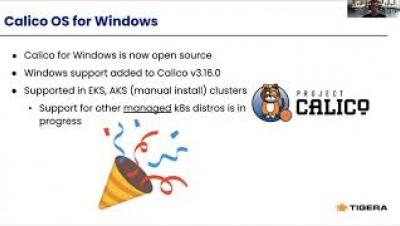
How to Secure Mixed Linux/Windows Clusters with Calico Policy
Rancher Recognized as a Leader in Latest Forrester Wave
The enterprise Kubernetes management space has definitely become a lot more crowded over the past two years as traditional vendors and startups alike attempt to grab a slice of this massive market. The increasingly competitive vendor landscape makes Forrester’s recent recognition of Rancher Labs that much more meaningful.
What is Docker Monitoring?
We have come a long way in the world of computing. From having computers that fill up entire rooms or buildings while performing relatively basic actions to having complex machines that literally fit in our pockets and palms, this advancement has been nothing short of breathless. With an emphasis placed on speed and efficiency, computers and the applications running on these computers have been tailored to ensure optimal use of resources, be these resources hardware or software resources.
Secure and monitor AWS Outposts and hybrid clouds
Today we announced that Sysdig has demonstrated successful integration of our monitoring and security software with AWS Outposts and achieved the AWS Outposts Ready designation. AWS Outposts provides a fully managed service that extends AWS infrastructure, services, APIs, and tools to your datacenter, co-location space or “edge” location to support on-prem and hybrid cloud use cases. AWS Outposts provides a hardware and software stack built on Amazon’s EC2 public cloud expertise.
An Introduction to Kubernetes and Its Uses
It's easy to get lost in today's continuously changing landscape of cloud native technologies. The learning curve from a beginner's perspective is quite steep, and without proper context it becomes increasingly difficult to sift through all the buzzwords. If you have been developing software, chances are you may have heard of Kubernetes by now. Before we jump into what Kubernetes is, it's essential to familiarize ourselves with containerization and how it came about.
Is Kubernetes Delivering on its Promise?
A headline in a recent Register article jumped off my screen with the claim: “No, Kubernetes doesn’t make applications portable, say analysts. Good luck avoiding lock-in, too.” Well, that certainly got my attention…for a couple of reasons. First, the emphasis on an absolute claim was quite literally shouting at me. In my experience, absolutes are rare occurrences in software engineering. Second, it was nearly impossible to imagine what evidence this conclusion was based on.
Announcing eBPF Mode GA
A few days ago, our team released Calico v3.16. As part of that release, we have marked the eBPF dataplane as “GA”, signalling that it is now stable and ready for wider use by the community. In this blog post I want to take you through the process of moving from tech-preview to GA.