Operations | Monitoring | ITSM | DevOps | Cloud
Management and Monitoring Tool that complements Azure Portal - Serverless60
10 new gems in Serverless360 | Webinar
Azure Service Bus, better managed and monitored using Serverless360
Azure Logic App, better managed and monitored using Serverless360
kr8 - Configuration Management for Kubernetes Cluster
This article originated from http://leebriggs.co.uk///blog/2018/11/07/kr8-kubernetes-config-mgmt.html Previous visitors to this blog will remember I wrote about configuration mgmt for Kubernetes clusters, and how the space was lacking. For those not familiar, the problem statement is this: it’s really hard to maintain and manage configuration for components of multiple Kubernetes clusters.
SecOps for the Cloud: PagerDuty and AWS Security Hub
This week at re:Inforce in Boston, the AWS team showed off its Security Hub service—a powerful service that provides SecOps teams a comprehensive view of their high-priority security alerts and compliance status across their AWS accounts. We’re excited to join AWS at re:Inforce this week as a Security Hub partner, where we’ll show users how PagerDuty and AWS Security Hub work together to provide real-time SecOps to any team using AWS.
Making Instrumentation Extensible
Observability-driven development requires both rich query capabilities and sufficient instrumentation in order to capture the nuances of developers’ intention and useful dimensions of cardinality. When our systems are running in containers, we need an equivalent to our local debugging tools that is as easy to use as Printf and as powerful as gdb.
Glitch List: June 2019
To keep you up-to-date with what’s going on in anomaly detection, we keep an ongoing list of the biggest glitches happening in the business world. Here is what made waves in June. June 25, 2019 When Dutch telco KPN suffered a major outage on the evening of Tuesday, June 25, the 112 emergency number was also knocked out across the country. “We have no reason to think it was (a hack) and we monitor our systems 24/7,” the company spokesperson told Reuters.
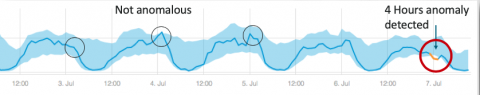
Amazon Quicksight ML Anomaly Detection vs. Anodot Autonomous Analytics
Companies invest in anomaly detection in order to proactively identify risks, such as revenue loss, customer churn and operational performance issues. Anomaly detection essentially enhances traditional BI and visualization tools, venturing beyond a summary view of your data. It constantly scans every metric, at a granular level, to find abnormalities. But in order for this technology to have an impact, you must be able to trust it.