Operations | Monitoring | ITSM | DevOps | Cloud
SCOM
The latest News and Information on Service Center Operations Manager and related technologies.
The Big SCOM Survey 2022 - 2023
The Big SCOM SURVEY is up and running viral again across the entire SCOM community. SCOM lovers of all regions and countries gather for this yearly event to share their perceptions, usage, and plans for Microsoft System Center Operations Manager. This year is the third round of the Big SCOM survey, conducted by SCOMathon, the learning and community hub for all SCOM-related topics.
Bad Observability
Observability has become a bit of a buzzword in the industry for the last few years. Exactly what "observability" means depends on who you ask, but most people would agree its about both: There's plenty of content out there telling you how to implement observability, or what good looks like. But what about bad observability? What are some anti-patterns to watch out for?
Grafana vs. Power BI vs SquaredUp
You’re part of a data-driven engineering team. You have a rich, complex, and dynamic set of tools but you’re struggling to discover and share insights from all that data. So, you're looking for a platform that will help unify it all. Naturally, you want to compare Grafana vs. Power BI - the big names. Plus, there's a new player on the block - SquaredUp.
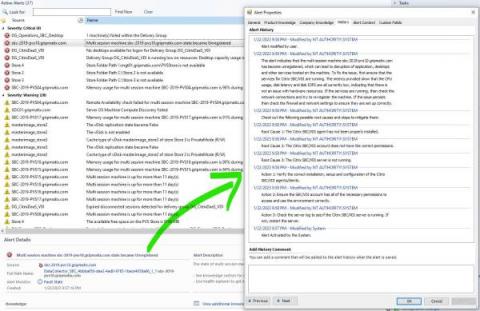
SCOM integration with OpenAI Chat GPT
We are happy to announce that we have created a SCOM integration with OpenAI Chat GPT. The solution checks for any alert generated in SCOM and then requests the artificial intelligence service to give you possible root causes and fixes to solve the issue. Moreover, it will take into account any other issues the respective degraded component or service is experiencing and consult you accordingly.
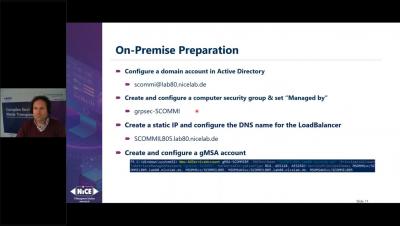
NiCE Oracle Management Pack 5.3 released
Oracle is a highly performant and reliable multi-model database management system running online transaction processing, data warehousing, and mixed database workloads. Although Oracle environments are reliable and performant, monitoring dedicated Oracle on-premise or cloud deployments is crucial to safeguard business continuity.
Dashboard Fridays: Sample Kubernetes dashboard
Dashboard Fridays: Sample Azure Monitor Dashboard
Dashboard Fridays: Sample Kubernetes dashboard
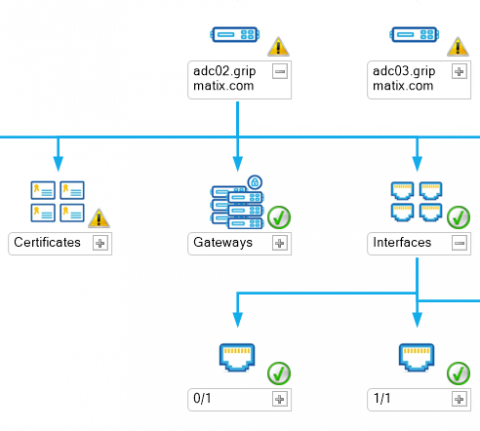
Your PKI infrastructure is worthless if ...
A common mistake IT organizations make, is having a well-designed Public Key Infrastructure (PKI), but at the same time having client devices, such as monitoring agents for your Citrix NetScalers, which accept to set up any encrypted connection, to any device, no matter what certificate they are presenting. In this case, you basically allow connections to be made to devices you do not know whether they can be trusted. This makes you vulnerable for 'spoofing'.