Operations | Monitoring | ITSM | DevOps | Cloud
Getting started with adding a new security data source in your Elastic SIEM: Part 1
What I love about our free and open Elastic SIEM is how easy it is to add new data sources. I’ve learned how to do this firsthand, and thought it’d be helpful to share my experience getting started. Last October, I joined Elastic Security when Elastic and Endgame combined forces. Working with our awesome security community, I’ve had the opportunity to add new data sources for our users to complement our growing catalog of integrations.
Virtual Meetup: SIEM 101: What, Why & How of Information Security
A Journey of Elastic SIEM: Getting Started through Threat Analysis Part 1
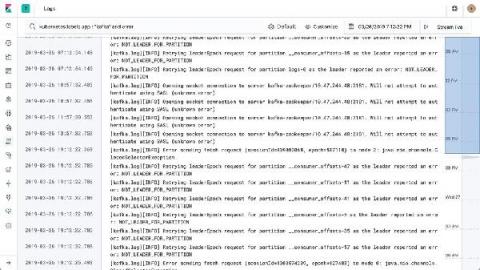
5 Reasons You Should Start Analyzing Your Logs
Integration and Shipping Okta Logs to Logz.io Cloud SIEM
Company security usually depends on your ability to come up with a diverse set of passwords and then manage them. Remembering all of them is considered a tad too difficult for most mere mortals, so a number of password storage apps have emerged. But they too have to be secured, and ultimately results in inefficient access and flawed security. Single-sign on (SSO) is still preferred, but to make it effective, companies like Okta have to secure integration across a number of apps.
Best Log Management Tools in 2020, and How to Select One for Your Organization
Generating MITRE ATT&CK® signals in Elastic SIEM: Sysmon data
Many mature security teams look to the MITRE ATT&CK® matrix to help improve their understanding of attacker tactics, techniques, and procedures (TTPs) and to better understand their own capabilities relative to these common adversarial approaches. With the release of Elastic Security 7.6, Elastic SIEM saw 92 detection rules for threat hunting and security analytics aligned to ATT&CK.
Elastic SIEM is free and open for security analysts everywhere
Security teams must protect attack surfaces that are becoming bigger and more distributed due to the growth of remote work, cloud infrastructure, and other dynamics. These teams understand that meeting this challenge at scale requires the successful incorporation of the appropriate technology into their security operations program.
The Cost of Doing SIEM & Security Analytics on Your Own
Security information and event management, or SIEM, has become part of the vocabulary of every organization. SIEM solutions gather events from multiple systems and analyze them—both in real time and through historical data. SIEM costs—as cyber security costs in general—can be high, but there is a tradeoff if you opt for the FOSS route (free and open source solutions).