California trucking company Quik Pick Express handles downtime and troubleshooting issues using OpManager
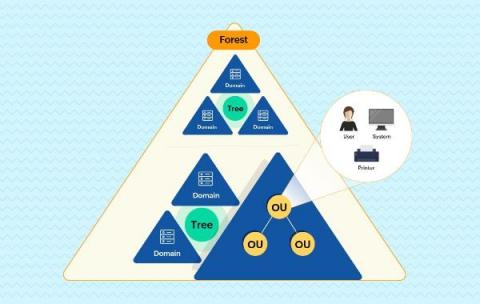
Quik Pick Express, a California-based trucking company, provides a variety of services, including container drayage, warehousing services, container shipping, transloading, and much more. The company services seven locations in the state of California, with its IT infrastructure network being critical for its business. After a thorough evaluation, Quik Pick Express’ IT team chose OpManager, an all-inclusive network monitoring solution, to monitor its business-critical IT infrastructure network.