Operations | Monitoring | ITSM | DevOps | Cloud
January 2022
Grafana Tempo 1.3 released: backend datastore search, auto-forget compactors, and more!
Grafana Tempo 1.3 has been released! We are proud to add the capability to search the backend datastore. This feature will also appear soon in Grafana Cloud Traces. If you want to dig through the nitty-gritty details, you can always check out the v1.3 changelog. If that’s too much, this post will cover the big ticket items. You can also register for our upcoming webinar “Distributed tracing in Grafana: From Tempo OSS to Enterprise” on Jan.
Adaptive Sampling in Jaeger
In distributed tracing, sampling is frequently used to reduce the number of traces that are collected and stored in the backend. This is often desirable because it is easy to produce more data than can be efficiently stored and queried. Sampling allows us to store only a subset of the total traces produced.
Ask Miss O11y: Observability Without Manual Tracing
TL;DR: Use auto-instrumentation from OpenTelemetry. Traces will happen. Then your code can use global library functions to customize those traces with your specific important data.
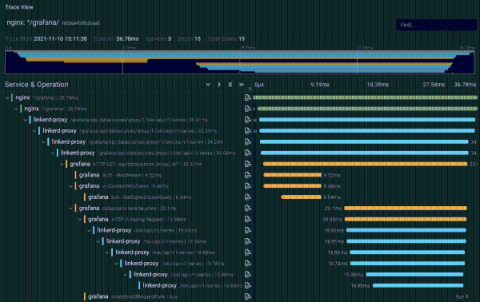
Configuring Grafana Tempo and Linkerd for distributed tracing
Anders Østhus is a DevOps Engineer on the Digital Tools team at Proactima AS, a consulting firm based in Norway that offers services and expertise in risk management, cybersecurity, healthcare, environmental solutions, and more. It can be difficult to orient yourself in the distributed tracing space, and getting all the parts of a tracing setup to play well with each other can be a bit tricky. But the benefits of tracing are undeniable.
What Is Auto-Instrumentation?
In the past, we’ve written about what instrumentation is and the insights it provides. Instrumenting your code generates telemetry that shows you how your system is performing, and whether your system is healthy. Like with most other companies, at Honeycomb we don’t write all of the code that runs in our systems.
Gain the upper hand over adversaries with Osquery and Elastic
With the Elastic 7.16 release, Osquery Manager is now generally available for Elastic Agent, making it easier than ever to deploy and run Osquery across your environments. By collecting Osquery data and combining it with the power of the Elastic Stack, you can greatly expand your endpoint telemetry, enabling enhanced detection and investigation, and improved hunting for vulnerabilities and anomalous activities.