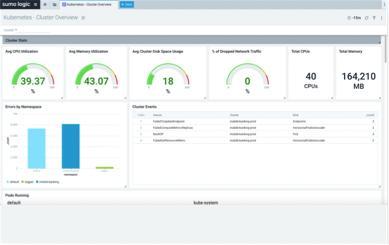
AWS Observability: Troubleshooting an issue
Learn how to use the Sumo Logic AWS Observability solution to troubleshoot an issue. Identify the problem by identifying an alerting metric, apply filters to isolate the issue, and pivot to related logs to verify the root cause.