How to Monitor User Permissions on Linux Servers With SolarWinds Server Configuration Monitor
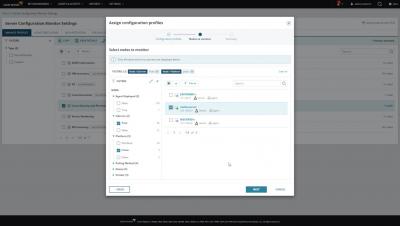
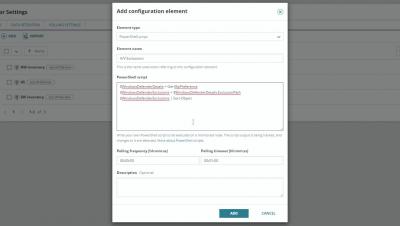
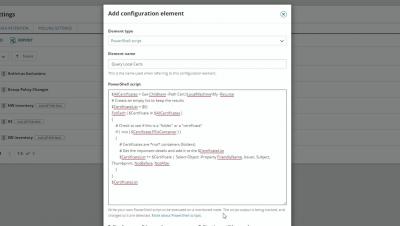
Understanding who has permissions to what and how those permissions levels change over time is an important piece of the puzzle when it comes to protecting sensitive data from getting into the wrong hands. However, this can be a difficult task when dealing with permissions on Linux servers and files. In this video, we'll show you how you can see who has access on your Linux servers, monitor and alert on changes to those permissions, and track the changes over time for auditing purposes.