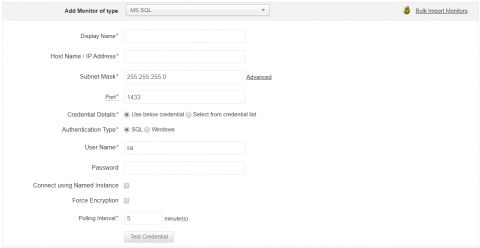
SQL Server, Part 2: Authentication and authorization mechanisms in SQL Server, simplified
In the previous blog of this series, we discussed how monitoring SQL Server activities helps secure databases. The database security can further be reinforced by carefully configuring the authentication and authorization mechanisms for database accesses. In this blog, we’ll briefly explain the various authorization and authentication mechanisms of SQL Server and some best practices you can follow.