Operations | Monitoring | ITSM | DevOps | Cloud
The 7 Hues of DevOps
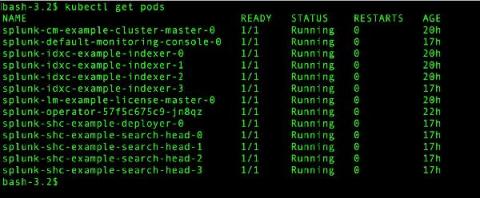
Going Live: Splunk Operator for Kubernetes 1.0.0
With everything going on in the world, it seems like a lifetime ago that we started talking about the Splunk Operator for Kubernetes, which enables customers to easily deploy, scale, and manage Splunk Enterprise on their choice of cloud environment. During that time, we’ve heard from an increasing number of on-premise and public cloud Bring-Your-Own-License Splunk customers that containerization and Kubernetes are an important part of their current and future deployment plans.
Monitoring Pulse Connect Secure With Splunk (CISA Emergency Directive 21-03)
To immediately see how to find potential vulnerabilities or exploits in your Pulse Connect Secure appliance, skip down to the "Identifying, Monitoring and Hunting with Splunk" section. Otherwise, read on for a quick breakdown of what happened, how to detect it, and MITRE ATT&CK mappings.
Elevate Your Cloud Security Posture with Splunk and Google Cloud
It’s more critical than ever to secure your company data and protect your workloads in the cloud. This blog post is a roundup of the latest technical resources and product capabilities by both Google Cloud and Splunk to enhance your threat prevention, detection, and response techniques, regardless of where you are in your business-transforming cloud journey.
Up Close Monitoring with SignalFlow
It’s April, and that means it’s Mathematics and Statistic Awareness month. And in our everyday world of monitoring and observability, both play an ever-increasing role in how we keep track of our environments, both our apps and our infrastructure. Our world is no longer about just pinging the server/app to make sure “It’s alive!”.
Introducing Splunk Attack Range v1.0
The Splunk Attack Range project has officially reached the v1.0 release. By achieving this milestone, we wanted to reflect on how we got here, what features we’ve built for v1.0 and what the future looks like for Splunk Attack Range. What is the Splunk Attack Range? 🧐
Up Close Monitoring with AWS Fargate
On our cloud-native journey, we live in a containerized world. Our environments are containers, managed by orchestrators, and living on some level of computing clusters. Of course, that means you are also responsible for managing all those bits, right?
Getting Started with the Splunk Distribution of OpenTelemetry Python
In our last blog, we introduced OpenTelemetry Python v1.0.0 and walked you through instrumenting a Python application and install both the OpenTelemetry API and SDK.
New Splunk Synthetic Monitoring Features Help Integrate Uptime and Performance Across the Entire Splunk Platform
For teams that build or maintain modern applications with their end-users in mind, the acquisition of Rigor means that Splunk now offers the most comprehensive synthetic monitoring solution on the market. Rigor, now Splunk Synthetic Monitoring and Web Optimization, provides best-in-class synthetic monitoring capabilities enabling IT Ops and engineering teams to detect and respond to uptime and performance issues within incident response coordination and throughout software development lifecycles.