Operations | Monitoring | ITSM | DevOps | Cloud
How to Track and Enforce Snyk Scans Across Your Production Environments
If you’re delivering software in a regulated environment, or deploying to a critical application or device, ensuring the security of your software code and dependencies is essential. One of the most popular tools for achieving this is Snyk, which gives developers the ability to find and fix vulnerabilities as part of their development workflow.
How to record a business process with Kosli's Audit Trail
Have you ever needed to provide proof that a critical business process actually took place? It’s a painful process involving all kinds of paperwork, but it’s the reality for many organizations working in highly regulated industries. For these companies, records need to be kept for actions like the provisioning of user accounts and access to sensitive records. It’s necessary, but it’s manual and time-consuming work.
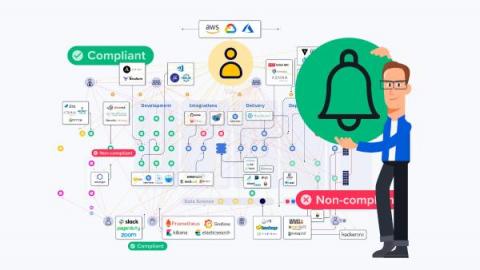
Stay on top of every change with Kosli Notifications
In this short blog, you will learn how to set up Kosli Notifications so your whole team can stay on top of environment changes and compliance events in real time. 🚀 In fast-paced technology landscapes, understanding how systems are changing is crucial. Developers, DevOps/Platform/SRE teams, security personnel, and management all need this information to manage operational risk, resolve incidents, and just for basic communication with each other.
From Monitoring to Action - Get Faster Incident Response with Change Forensics
In this post you’ll learn how Kosli’s Change Forensics gives DevOps, Platform, and Site Reliability Engineers the ability to rapidly pinpoint and understand changes and events in their infrastructure and applications, and get to the cause(s) of an incident quickly.
How to record events in your CI pipelines with Kosli Flows
In an ideal world CI pipelines would never fail and deployments would be easy to navigate. The reality is that the journey from commit to production can fail in subtle ways that can be hard to understand. And this problem is multiplied by the number of pipelines in your system.
Data Tampering: A Comprehensive Guide
In an increasingly interconnected and data-driven world, where information shapes decisions and fuels innovation, the integrity of data has become paramount. However, lurking beneath the surface is a silent threat that can undermine trust, compromise systems, and wreak havoc on organizations: data tampering. In this post, we delve into the realm of data tampering, exploring the vulnerabilities, the reasons behind data tampering practices, and countermeasures against them.
CRLF Injection, Explained: An In-Depth Guide
In this in-depth guide we’ll explore CRLF injection, a web application security vulnerability that can have severe consequences. First, we’ll cover what CRLF injection is, the types of CRLF injection attacks, and their potential impacts. Additionally, we’ll discuss similarities with other attacks, payloads used in these exploits, and how to prevent CRLF injection. Finally, we’ll touch on the role of OWASP in addressing this security risk.
Terraform Import: What It Is and How to Use It
In this post we’ll explore Terraform Import, a powerful command-line tool that allows you to bring existing infrastructure under Terraform management. We’ll cover what Terraform Import is, its common use cases, and how to use it effectively. Additionally, we’ll discuss some limitations you should be aware of when using Terraform Import.
The Dark Side of DevSecOps and the case for Governance Engineering
For today’s software organizations security has never been more top of mind. On one side there is the present and growing threat of being hacked by malicious actors, set out in Crowdstrike’s recent Global threat report. And, on the other, there is a wave of cybersecurity regulation from the government to mitigate such cybersecurity vulnerabilities.