Operations | Monitoring | ITSM | DevOps | Cloud
Detecting CVE-2020-14386 with Falco and mitigating potential container escapes
On September 14, CVE-2020-14386 was reported as a “high” severity threat. This CVE is a kernel security vulnerability that enables an unprivileged local process to gain root access to the system. CVE-2020-14386 is a result of a bug found in the packet socket facility in the Linux kernel. It allows a bad actor to trigger a memory corruption that can be exploited to hijack data and resources and in the most severe case, completely take over the system.
Microk8s and Charmed ceph at the edge
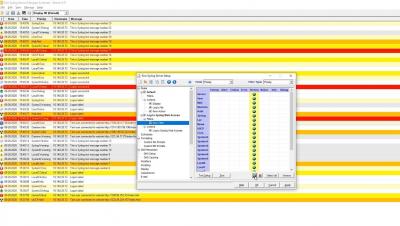
Server Monitoring with OpsRamp
For decades, compute or server infrastructure has been the backbone of the IT world. Compute has gradually evolved from on-premise hardware to programmable compute in the form of software containers. Technology operators need to constantly monitor the performance of their Windows, Linux, and container infrastructure so that they can optimize their compute environments to match workload demands.
Security corner: snap interface & snap connections
One of the defining features of snaps is their strong security. Snaps are designed to run isolated from the underlying system, with granular control and access to specific resources made possible through a mechanism of interfaces. Think of it as a virtual USB cable – an interface connects a plug with a slot. Security and privacy conscious users will certainly be interested in knowing more about their snaps – what they can do and which resources they need at runtime.
An Introduction to Testing Robot Code
The myriad of different fields that make up robotics makes QA practices difficult to settle on. Field testing is the go-to, since a functioning robot is often proof enough that a system is working. But online tests are slow. The physical environment must be set up. The entire system has to be in a workable state. Multiple runs are needed to build confidence. This grinds development to a halt.
The State of Robotics - August 2020
So that’s the summer gone (hopefully, that heat was awful). Or winter if that’s where you are. Seasons change and so does the state of robotics. Fortunately, that’s what we’re here for. Before we get into it, as ever, If you’re working on any robotics projects that you’d like us to talk about, be sure to get in touch.
Become FIPS Compliant with HAProxy Enterprise on Red Hat Enterprise Linux 8
Guarantee strong encryption by enabling ‘FIPS mode’ with RHEL and HAProxy Enterprise. SSL and its successor TLS are protocols that safeguard web traffic as it crosses the Internet, encrypting communication and protecting it from tampering. However, the encryption algorithms within these protocols are subject to change over time as vulnerabilities are discovered or as better encryption methods become available.
How Canonical remotely delivers and supports customer cloud deployments
The widespread shift to remote working in response to the COVID-19 pandemic has been a disruptive change for countless businesses; some 13% of organisations say they have faced major disruption. But at Canonical, remote working has long been the status quo for many of our teams. In spite of the challenging circumstances in which we all find ourselves, Canonical has been able to continue to operate and support our customers despite their working practices undergoing significant changes.