Flowmon and WhatsUp Gold: Automatic Threat Detection Through Single Pane of Glass
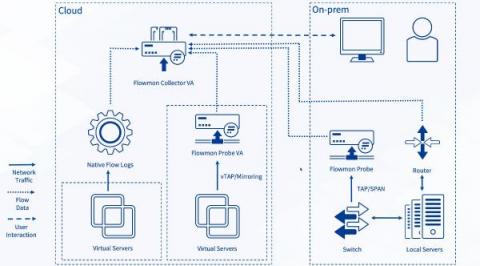
Network Detection & Response (NDR) is a key element that provides an additional level of security across the company wide network through detection of threats that bypass traditional security measures and materialize in the company’s digital environment. Progress Flowmon ADS (Anomaly Detection System) is a typical representative of an NDR system that combines various detection techniques to ensure that malicious activity is recognized and flagged as a security incident.