Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
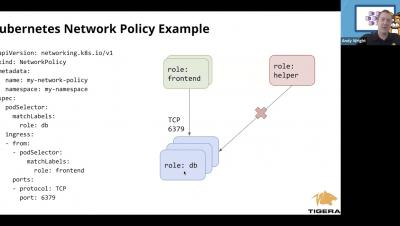
How to Implement Network Policy in Amazon EKS to Secure Your Cluster
How to Deploy an Azure Kubernetes Cluster with AKS
At the end of October 2017, Microsoft announced the release of Azure Kubernetes Service (AKS), its hosted version of Kubernetes. If you’re new to AKS and curious about how to get a proof of concept (PoC) set up in your environment, read on. In this AKS tutorial, you’re going to learn, step-by-step, how to get an Azure Kubernetes cluster built with AKS.
Master Class - PCI Compliance and Vulnerability Management for Kubernetes - 2020-05-05
Kubernetes Master Class - Understanding Upgrades and Rollbacks in Rancher 2.4
Local Kubernetes Development with Okteto
At Codefresh we understand how much Kubernetes has changed the local flow for developers and we have already covered not only local Kubernetes distributions for Mac, Windows and Linux, but also specialized tools such draft, skaffold, garden.io and tilt.dev that are focused on developers who work with Kubernetes. This time we will look at Okteto, a brand new tool that aims to make developers more productive when using Kubernetes.
Kubernetes and the Enterprise Knowledge Graph
In today’s enterprises, we spend much of our time dealing with information, whether it’s data, knowledge or analytics. Just like the assembly line workers of last century, today’s knowledge workers deal with similar logistics of taking raw materials as an input and producing a finished product as an output. Only in this case, the raw material is all the unorganized and sometimes random information at our disposal, and the finished product is structured information.
How to Implement Network Policy in Azure AKS to Secure Your Cluster
Secure DevOps at the Edge with Sysdig and IBM
Innovative companies are looking to take advantage of cloud-native technologies beyond the data center to deliver faster innovation and competitive advantage at the edge. Recognizing the need for a common approach to create, deploy, run, secure, monitor, maintain and scale business logic and analytics applications wherever your business takes you, IBM today announced its edge computing offerings, including the IBM Edge Application Manager.
Deploying Citrix Ingress Controller via the Rancher Catalog
Citrix Ingress Controller is an emerging enterprise-grade ingress controller for load balancing microservices in the Kubernetes environment. It provides advanced load balancing, rewrite/responder policy support, advanced content routing, SSL/TLS support, TCP/UDP protocol support, Canary deployment support and much more. In this article, we will discuss different deployment modes for Citrix Ingress Controller and deploy it via the Rancher catalog.