Operations | Monitoring | ITSM | DevOps | Cloud
Sysdig Teams
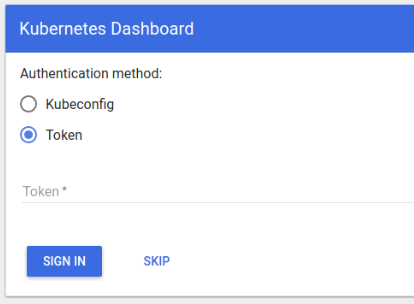
CVE-2018-18264 Privilege escalation through Kubernetes dashboard
A recently disclosed vulnerability in Kubernetes dashboard (CVE-2018-18264) exposes secrets to unauthenticated users. In this blog post we’ll explore some key takeaways regarding monitoring privilege escalation on Kubernetes.
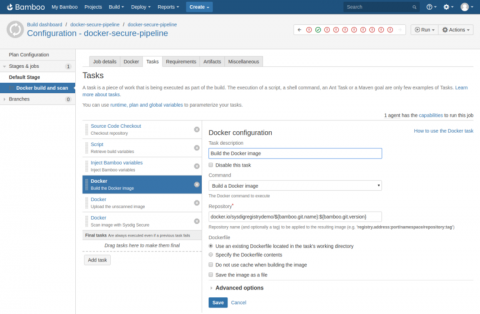
Integrating Sysdig Secure with Atlassian Bamboo CI/CD
In this blog post we are going to cover how to perform Docker image scanning on Atlassian’s Bamboo CI/CD platform using Sysdig Secure. Container images with security vulnerabilities or not compliant with the security policies that you define within Sysdig Secure will be stopped, breaking the build pipeline before being pushed to your Docker registry.
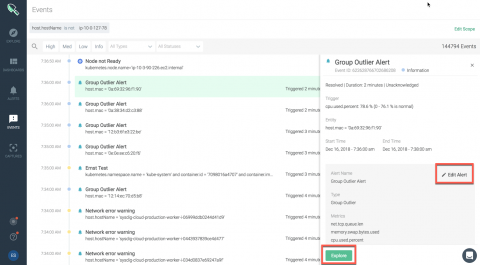
Unveiling Sysdig Monitor Events
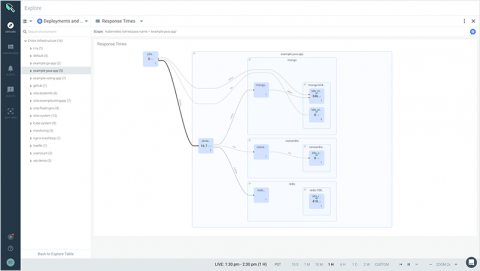
At Sysdig, we have built a cloud-native intelligence platform to create a single, more effective way to monitor and secure your critical applications. We want to empower our users to quickly identify critical events and focus on events that need the most attention from you.
Now Available: IBM Cloud Monitoring with Sysdig.
Today at Kubecon we announced the availability of IBM Cloud Monitoring with Sysdig. Together, IBM and Sysdig have launched this new offering to provide a fully managed enterprise-grade monitoring service for cloud-native applications on IBM Cloud. If you build, ship, and run applications on IBM Cloud, you now have direct, integrated access to Sysdig Monitor.
Introducing Sysdig Secure 2.2: Kubernetes auditing, compliance, and access control.
Over the past four years we’ve helped hundreds of organizations run reliable, secure, and compliant Kubernetes and Openshift clusters. Some of the key themes we’ve seen from organizations that have successfully grown their Kubernetes footprint are: they have immaculate labeling, understand how to leverage internal Kubernetes features to harden their platform, and understand what developers need access to and manage it with RBAC and namespaces.
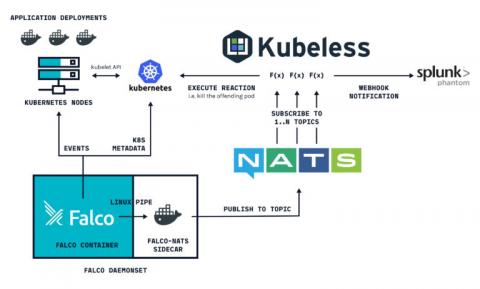
Container security orchestration with Falco and Splunk Phantom
Container security orchestration allows to define within your security policy how you are going to respond to your different container security incidents. These responses can be automated in what is called security playbooks. This way, you can define and orchestrate multiple workflows involving different software both for sourcing and responding. This is how Falco and Splunk Phantom can be integrated together to do this.
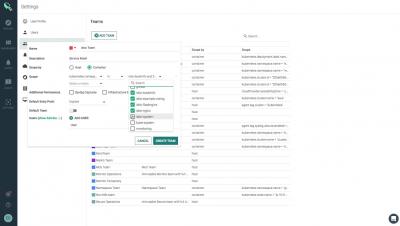
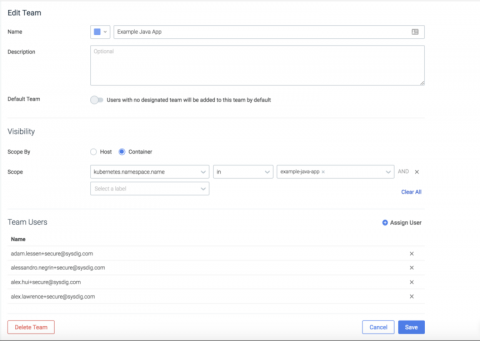
Service based access control with Sysdig Secure Teams
While you’re likely familiar with role-based access control, Sysdig teams introduce the concept of service-based access control. With service-based access control, administrators can define groups of users that have access to policy events, policy configuration, and scanning data limited to a service or set of services, as defined by your orchestration system (think Kubernetes, Mesos, and the like).
How to identify malicious IP activity using Falco
One of the most common security use cases, is the ability to identify connections generated by malicious actors, or internal components connecting to suspicious servers (e.g malware C&Cs). In this post, we will show how to leverage the Falco engine, to identify connections made to IPs that were flagged by multiple security sensors, and are streamed as a feed to the Falco engine.