Operations | Monitoring | ITSM | DevOps | Cloud
Sysdig Monitor: Creating Alerts from Events
Sysdig Monitor: Creating Alerts from scratch
Sysdig Monitor: Time & Group Aggregation
ContainerD meets Sysdig
Containers are fast becoming the defacto standard as a building block for creating and deploying applications. Containerization allows development teams to have consistent environments, cost optimizations, isolation, and versatility, in general. The open-source Containerd project is a critical component for the modern cloud-native containerized landscape, providing a runtime that is widely used in millions of applications every day.
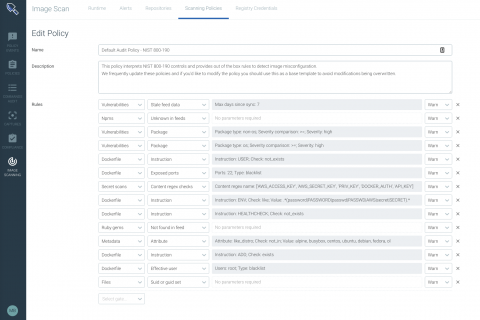
Announcing Sysdig Secure 2.3: NIST + PCI image compliance checks, Kubernetes and Docker remediation tips, and more!
Today we are very excited to announce our latest release — Sysdig Secure 2.3! In this version of Sysdig Secure, we have invested heavily in hardening the compliance posture of Kubernetes, Docker configurations, and container images. We have released a set of features that provide compliance focused image scanning, guided remediation, compliance dashboards, and more.
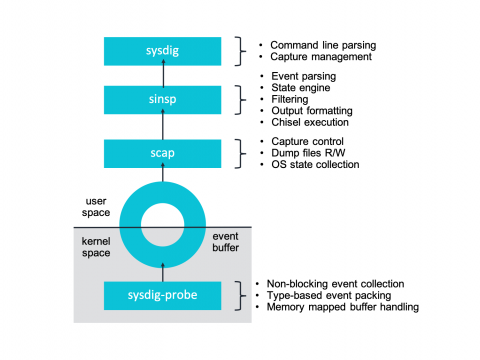
Sysdig and Falco now powered by eBPF.
At Sysdig we’ve recently undergone a pretty interesting shift in our core instrumentation technology, adapting our agent to take advantage of eBPF – a core part of the Linux kernel. Sysdig now supports eBPF as an alternative to our Sysdig kernel module-based architecture. Today we are excited to share more details about our integration and the inner workings of eBPF. To celebrate this exciting technology we’re publishing a series of articles entirely dedicated to eBPF.
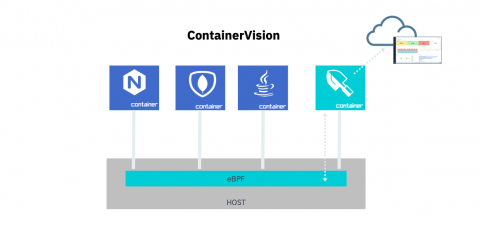
Introducing container observability with eBPF and Sysdig.
Today we’ve announced that we’ve officially added eBPF instrumentation to extend container observability with Sysdig monitoring, security and forensics solutions. eBPF – extended Berkeley Packet Filter – is a Linux-native in-kernel virtual machine that enables secure, low-overhead tracing for application performance and event observability and analysis.
Meet Sysdig
Sysdig and IBM to collaborate on IBM Cloud Private & IBM Multicloud Manager container monitoring and security
Today at Think 2019 we’re announcing our intent to work with IBM to support the Sysdig Cloud-Native Intelligence Platform on IBM Cloud Private and IBM Multicloud Manager. By supporting IBM Multicloud Manager and IBM Cloud Private, Sysdig will help IBM customers accelerate the transition to cloud architectures.