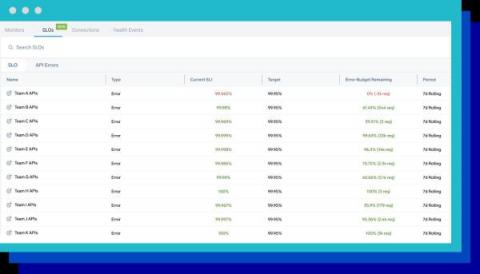
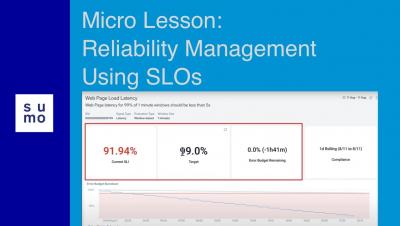
How to get maximum value from Service Level Objectives (SLOs)
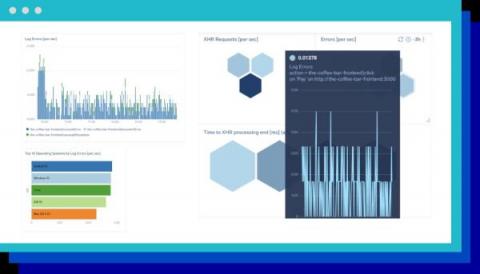
A reliable digital customer experience is critical to the success of digital-first businesses. Each minute of downtime can result in the loss of revenue, unsatisfied customers, and damage to reputation. However, as your uptime gets closer to 100%, it gets exponentially harder to improve and often comes at the cost of speed of innovation. A good balance between innovation (i.e., new feature releases) and maintaining an acceptable level of reliability is key to success in the digital world.