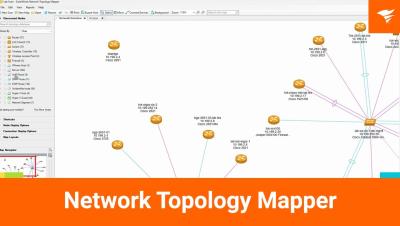
Getting Started with SolarWinds Network Topology Mapper
The video provides a quick walkthrough of the SolarWinds Network Topology Mapper, starting with the welcome screen that prompts users to run a new scan. It guides viewers through a wizard for adding SNMP credentials, emphasizing the importance of specifying IP addresses for accurate mapping. The tool can identify unmanaged switches and allows for both one-time scans and scheduled updates, maintaining a clean map by archiving previous scans. Users can hover over connections to view port numbers, although serial numbers remain unavailable. The presenter encourages viewers to reach out with any questions.