Operations | Monitoring | ITSM | DevOps | Cloud
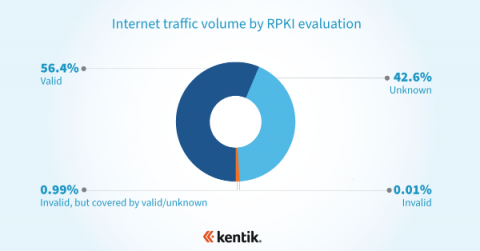
Measuring RPKI ROV adoption with NetFlow
Resource Public Key Infrastructure (RPKI) is a routing security framework that provides a mechanism for validating the correct originating autonomous system (AS) and prefix length of a BGP route. Route Origin Authorization (ROA) is a cryptographically signed object within the RPKI that asserts the correct originating AS and prefix length of a BGP route. For as long as the internet has existed, the challenge of securing its underlying protocols has persisted.
The evolution of network visibility
In the old days, it took a bunch of help desk tickets for an engineer to realize there was something wrong with the network. At that time, troubleshooting meant logging into network devices one-by-one to pore over logs. In the late 80s, SNMP was introduced giving engineers a way to manage network devices remotely. It quickly became a way to also collect and manage information about devices. That was a big step forward, and it marked the beginning of network visibility as we know it today.
Understanding data analysis and online activity with David Belson
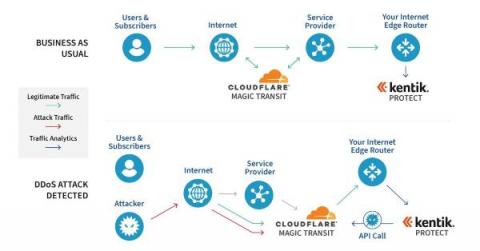
Working with Cloudflare to mitigate DDoS attacks
The rolling thunder of cybersecurity warnings has built to a crescendo this year. According to HelpNetSecurity, cybercriminals launched over 9.75 million DDoS attacks in 2022. The Cloudflare Attack Trends 2022 Q1 Report published yesterday shows an alarming increase in application-layer DDoS attacks. And our own Doug Madory has been sharing analysis on the impact of cyberattacks, too.
Network AF, Episode 13: Talking networking and PR with Ilissa Miller
In this episode of the Network AF podcast, Avi Freedman connects with Ilissa Miller, network whisperer and PR industry veteran. Ilissa and her team translate technology into business terms by helping clients understand the value and functionality of a company. Avi asks Ilissa how she got into the field, her biggest takeaways that helped launch her own business and what’s important in today’s networking world.
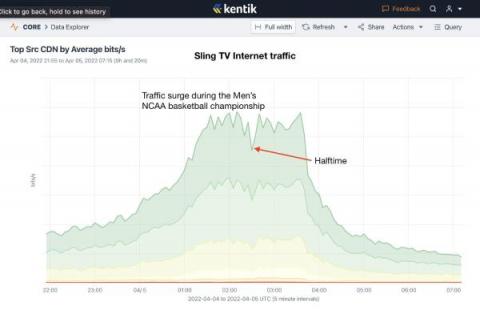
Anatomy of an OTT traffic surge: 2022 Men's NCAA Basketball Championship
Last night, Kansas topped the University of North Carolina in a thrilling come-from-behind victory to win their fourth championship in men’s college basketball. It was also notable in how viewers saw the game. Instead of being aired on CBS (network television), the game was carried on TBS requiring viewers to have either a cable TV package or use a streaming service to watch the game. Here’s what we saw.
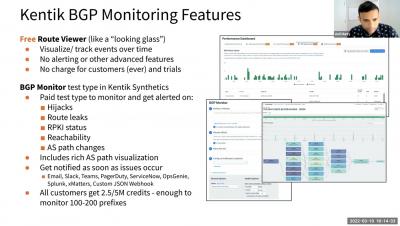
Why You Should Monitor BGP and Where to Start 031122
Synthetics 101 - Part 2: Protecting and growing revenue with proactive monitoring
In part 1 of our synthetics series, we looked at tracking network performance to drive better business outcomes. Here in part 2 of our series, we’ll dig into the very first and most basic business outcome of using digital experience monitoring (DEM). That is, we’ll look at how to protect and grow revenue by proactively monitoring the health, availability and uptime of your critical applications and services, so you can fix issues before your customers’ experience suffers.