Operations | Monitoring | ITSM | DevOps | Cloud
Configuring YAML Files after Installing the ELK Stack
What is YAML? YAML is a readable data serialization language used frequently in configuration files for software; it stands for “Ain’t Markup Language.” This article will show you samples of YAML files (written .yml or .yaml) for the ELK Stack and other programs commonly used by DevOps team. And while some people love yaml and some hate it, it’s not going away.
A List of the Best Open Source Threat Intelligence Feeds
Threat intelligence feeds are a critical part of modern cybersecurity. Widely available online, these feeds record and track IP addresses and URLs that are associated with phishing scams, malware, bots, trojans, adware, spyware, ransomware and more. Open source threat intelligence feeds can be extremely valuable—if you use the right ones. While these collections are plentiful, there are some that are better than others.
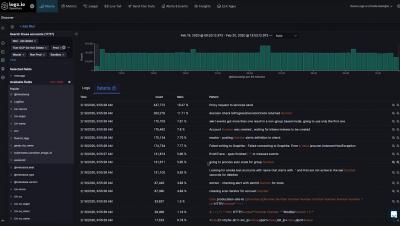
Integrating Palo Alto with Logz.io's Cloud SIEM
First things first, why would you want to collect logs from Palo Alto and send them to a Cloud SIEM? There are many reasons. At its core, having a centralized location with a consistent user experience for managing alerts, notifications, and information coming from the technologies securing your environment can provide value in a lot of ways. In this blog, we’ll discuss how to collect, parse, and analyze Palo Alto logs in Logz.io Cloud SIEM, and how it can help secure your cloud workloads.
Collecting and Shipping Kubernetes logs at scale with FileBeat Autodiscover
The Best Resources for Learning Kubernetes
Kubernetes is the world’s leading container orchestration platform. Its cloud agnostic status enables you to manage your workloads with ease, whether they reside in the cloud or on-premises. It has reduced the necessity of being locked into services provided by a cloud provider as well as the need for an entire operations team to manage large workloads on-premises on virtualization platforms.
OpenTracing, OpenCensus & OpenTelemetry: What is Distributed Tracing?
Software monitoring allows developers and IT professionals to observe events occurring within a monitored system. The data gathered by monitoring processes offers visibility into how the monitored entity is behaving and provides warning signs indicating that some aspect of the system deserves greater attention. More and more software is migrating to the cloud, and monolithic software is being decomposed into microservices to create distributed applications.
dormakaba EMEA Finds Reliable, Secure and Scalable Logging with Logz.io
As the team responsible for building dormakaba’s first cloud-access control solution, Exivo, the Cloud Development team at dormakaba AS EMEA needed a logging solution that with scalable logging throughout their global environment, handle a huge amount of throughput, be piped through an API, and remain highly secure so it could be implemented on the doors and entry systems the company produces. Logz.io was the perfect fit for these requirements.
Tutorial: Shipping AWS Kinesis Data Stream Logs to Logz.io
Kinesis is a managed, high-performance and large-capacity service for real time processing of (live) streaming data. Prominent users include Netflix, Comcast and Major League Baseball. Its design to let it grab data from multiple sources at the same time and to scale processing within EC2 instances.
Istio vs. Linkerd vs. Envoy: A Comparison of Service Meshes
In a previous article, we examined service meshes in detail. Briefly, a service mesh takes care of network functionality for the applications running on your platform. As Kubernetes has matured as a technology, service meshes have become a hot topic, with various products being developed to solve the challenges associated with areas like traffic management, security, and observability. This article will compare three service meshes.