Profiling "VIP Accounts" Part 1
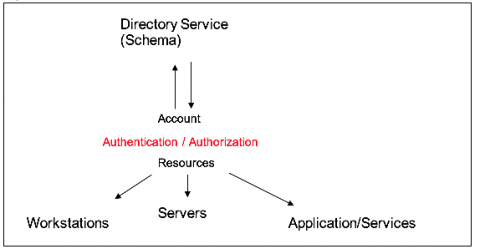
Detecting malicious activity is rarely easy, but some attacker methods are more challenging to detect than others. One of the most vexing techniques to counter is credential theft. Attackers that gain control over a user account have access to the assets of that user. If the credentials are for an account with special privileges, like a system administrator, then the attacker may be able to gain access to system-wide resources and even be able to change logs to cover their tracks.