Operations | Monitoring | ITSM | DevOps | Cloud
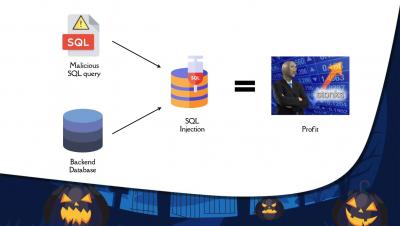
Halloween Cyber Street- SQL injections and cross site scripting attacks
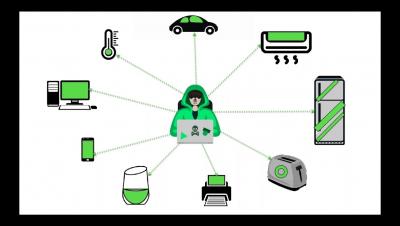
What is a DDOS attack- GitHub story and Mirai botnet.
Apple in 2018, now Tesla-who's next in the line of internal data leaks?
Recent allegations of an ex-Tesla employee syncing the Autopilot source code to his personal iCloud account is yet another classic case of how poor data security is, even in some of the most technologically advanced organizations. The Tesla leak isn’t even the first time that a data breach of such immense magnitude pertaining to self-driving technologies has occurred; in July 2018, an Apple employee was caught using AirDrop to transfer 40GB of confidential data to a personal PC.
IT analytics in 90 seconds: Monitor your inactive privileged users to mitigate security risks
Here's how Rojan, a leading MSP in Australia saves thousands on IT maintenance costs with OpManager
Rojan Australia Pty Ltd is a managed IT services provider that supports a wide assortment of customers and businesses, and provides services such as hosted Microsoft Exchange, Xen Citrix servers, rack space, internet links, and desktop support.
Five BYOD challenges IT teams face and ways to mitigate them
BYOD stands for bring your own device, whereby your organization lets employees use personal devices for day-to-day work. Sounds simple, right? Unlike corporate devices where the enterprise has complete freedom to choose users’ device types and platforms, BYOD is a different case altogether. In BYOD environments, employees often use different devices manufactured by different OEMs running on multiple OS versions.
ManageEngine recognized for Next Gen Unified Endpoint Management in London
“With cybercrime heading into the tens of billions of records stolen, and trillions of dollars in damages, we are proud to recognize ManageEngine as an award-winning innovator that offers a new approach to defeat these criminals,” said Pierlugi Paganini, editor-in-chief, Cyber Defense Magazine.
IT analytics in 90 seconds: Stay on top of unusual behavior in your privileged accounts
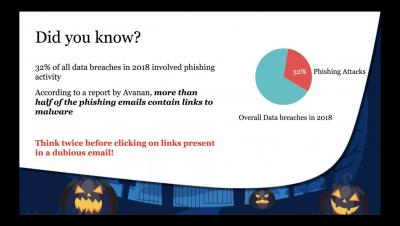
Beware of black cats and black hats this Halloween
It’s that time of the year again when you sport your favorite costume, carve pumpkins, gear up for trick-or-treating, and reread Gothic stories. It’s almost Halloween! There is no denying that October is all about ghosts and ghouls, tricks and treats, witches and wizards, pirates and pumpkins. However, October is also National Cybersecurity Awareness Month (NCSAM), a time to remember that alongside our cogent fears lies another reality that’s much more ghastly—cyberattacks.