Operations | Monitoring | ITSM | DevOps | Cloud
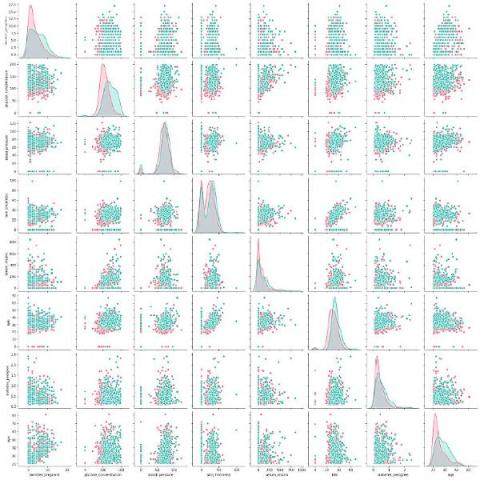
Visual Link Analysis with Splunk: Part 1 - Data Reduction
Recently, I presented at .conf20, Splunk’s annual user conference, on link analysis, where I promised more technical details on the topic in the coming weeks. To keep my promise, I’ve started a three-part series to show you how to use Splunk for link analysis.
Walkthrough to Set Up the Deep Learning Toolkit for Splunk with Amazon EKS
The Splunk Deep Learning Toolkit (DLTK) is a very powerful tool that allows you to offload compute resources to external container environments. Additionally, you can use GPU or SPARK environments. In last Splunk blog post, The Power of Deep Learning Analytics and GPU Acceleration, you can learn more about building a GPU-based environment. Splunk DLTK supports Docker as well as Kubernetes and OpenShift as container environments.
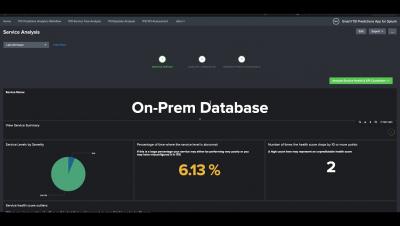
Get to Know Splunk Machine Learning Environment (SMLE)
One of our most exciting new projects at Splunk is coming to life. Over the past year, we have been hard at work putting together our vision: a place where Splunk admins, NOC/SOC teams, data analysts, and data scientists can collaborate, experiment, and operationalize their work, all in a single environment inside the Splunk ecosystem. We call it Splunk Machine Learning Environment (SMLE).
Splunk SOAR Playbooks: Finding and Disabling Inactive Users on AWS
Every organization that uses AWS has a set of user accounts that grant access to resources and data. The Identity and Access Management (IAM) service is the part of AWS that keeps track of all the users, groups, roles and policies that provide that access. Because it controls permissions for all other services, IAM is probably the single most important service in AWS to focus on from a security perspective.
What's Next for Department of Defense Digital Modernization?
As the Trump Administration comes to a close, there is no better time than the present to reexamine the Department of Defense Digital Modernization Strategy and its potential sustainment beyond January 2021.
Macros, We Don't Need No Stinking Macros! - Featuring the New Microsoft O365 Email Add-On
Recently, I’ve been on a mission building a new Microsoft Office 365 Email Add-on for Splunk. This has been built for use with Splunk Enterprise, while making sure that it properly supports Splunk’s Common Information Model (CIM). CIM is paramount when wanting data to play nicely with Splunk Enterprise Security.
Splunk SOAR Playbooks - AWS IAM Find and Disable Inactive Users
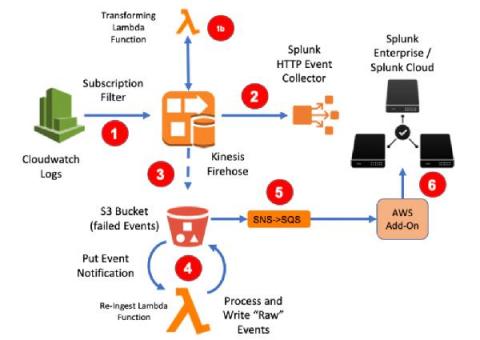
AWS Firehose to Splunk - Two Easy Ways to Recover Those Failed Events
With Kinesis Firehose being Splunk’s preferred option when collecting logs at scale from AWS Cloudwatch Logs, we’ve seen plenty of posts on setting this up, automation and examples on transforming event content. But what about when things go wrong?
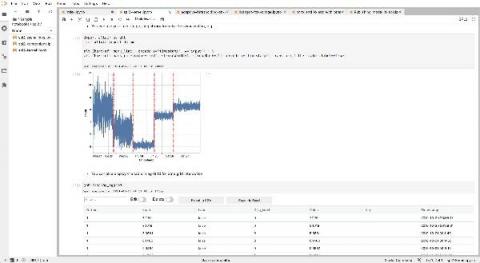
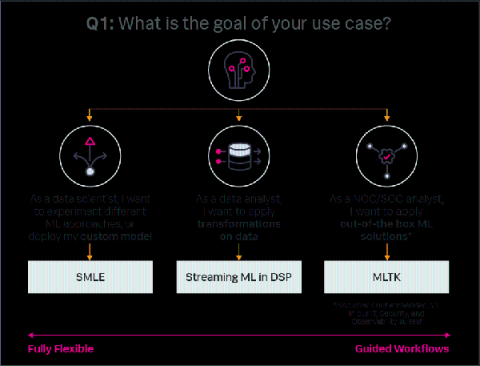
Machine Learning Guide: Choosing the Right Workflow
Machine learning (ML) and analytics make data actionable. Without it, data remains an untapped resource until a person (or an intelligent algorithm) analyzes that data to find insights relevant to addressing a business problem. For example, amidst a network outage crisis a historical database of network log records is useless without analysis. Resolving the issue requires an analyst to search the database, apply application logic, and manually identify the triggering series of events.