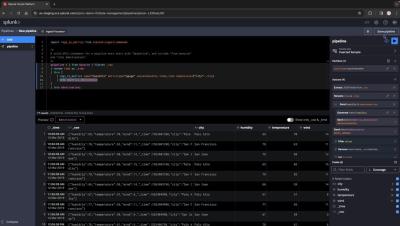
Create a Splunk Observability Cloud destination (with Voiceover)
Create a connection to your Splunk Observability Cloud deployment from the system connections page in Splunk Cloud Platform - now enhanced with voiceover narration to provide clearer instruction and improved accessibility.