Modern Phishing Is Slipping Past SOCs. Here's How to Stop It Early
Image Source: depositphotos.com
Most phishing attacks today do not look dangerous at first. They use trusted platforms, familiar login pages, and encrypted traffic that appears completely normal to security tools. For SOCs, that creates a serious operational problem: the team may see something suspicious, but confirming real risk often takes too long, giving attackers time to steal credentials and move into business-critical systems.
Closing that gap requires a different approach to phishing investigation. Here is how security leaders can help their SOC uncover hidden phishing behavior sooner, reduce investigation delays, and stop identity-driven attacks before they turn into wider business impact.
Phishing Techniques That Still Bypass SOC Workflows
Modern phishing campaigns are built to stay invisible long enough for attackers to capture credentials or hijack sessions. Instead of relying on obvious malware or suspicious domains, attackers use techniques that delay confirmation and make malicious activity appear routine.
Some of the most common examples include:
- QR code phishing (Quishing) that moves the attack flow outside the email environment
- Login pages hosted on trusted cloud infrastructure such as storage services and website builders
- Multi-step redirect chains that hide the final phishing destination
- Encrypted HTTPS sessions that conceal credential harvesting inside legitimate-looking traffic
- CAPTCHAs and interaction gates that prevent automated inspection tools from revealing the attack
When these techniques are combined, SOC teams often see the signal but lack immediate proof of malicious intent. Investigations take longer, alerts stay unresolved, and attackers gain time to test stolen credentials across SaaS, VPN, and cloud environments.
How SOC Teams Can Expose Hidden Phishing Behavior Earlier
Security leaders are increasingly adopting three capabilities that make early phishing confirmation possible:
Step #1: SSL Decryption. Exposing the Threat Behind Trusted Traffic
Modern phishing increasingly operates inside encrypted HTTPS sessions. Fake login pages, redirect chains, and credential-harvesting flows are delivered through legitimate infrastructure and protected by valid SSL certificates, making malicious activity look normal at first glance.
Automatic SSL decryption inside ANY.RUN’s interactive sandbox reveals what is actually happening during execution. By decrypting HTTPS traffic in real time, SOC teams can see malicious redirects, credential capture mechanisms, and attacker-controlled infrastructure that would otherwise remain hidden.
Check Real-World Salty2FA Phishing Analysis
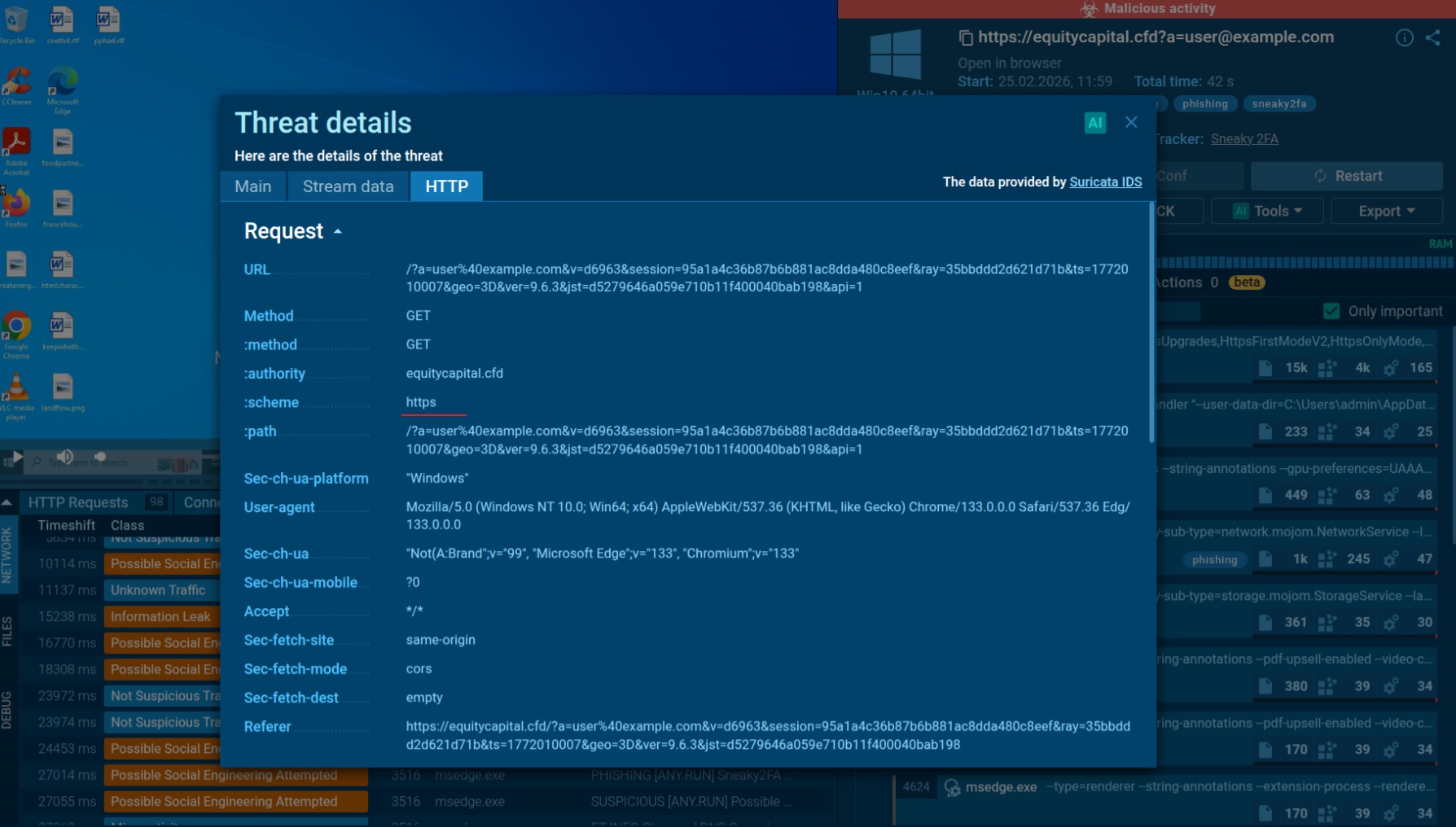
ANY.RUN sandbox provides connection details, showing HTTPS traffic
Outcomes for SOC teams:
- earlier confirmation of encrypted phishing attacks
- better visibility into credential harvesting and session hijacking
- less time spent validating suspicious HTTPS traffic
- stronger detection against phishing that hides behind trusted platforms
|
Reduce breach exposure and confirm phishing faster with investigation workflows proven to cut MTTR by 21 minutes. |
Step #2: Interactive Analysis. Seeing the Attack Before the User Does
Many phishing attacks reveal their real intent only after user interaction. Redirect chains, credential prompts, and malicious infrastructure often appear only after clicking through pages or entering login details.
Interactive sandbox analysis provided by ANY.RUN allows teams to safely execute suspicious links and interact with them as a user would. Instead of relying on reputation checks or metadata alone, analysts can observe the full phishing flow in a controlled environment in less than 60 seconds and confirm malicious behavior with real evidence.
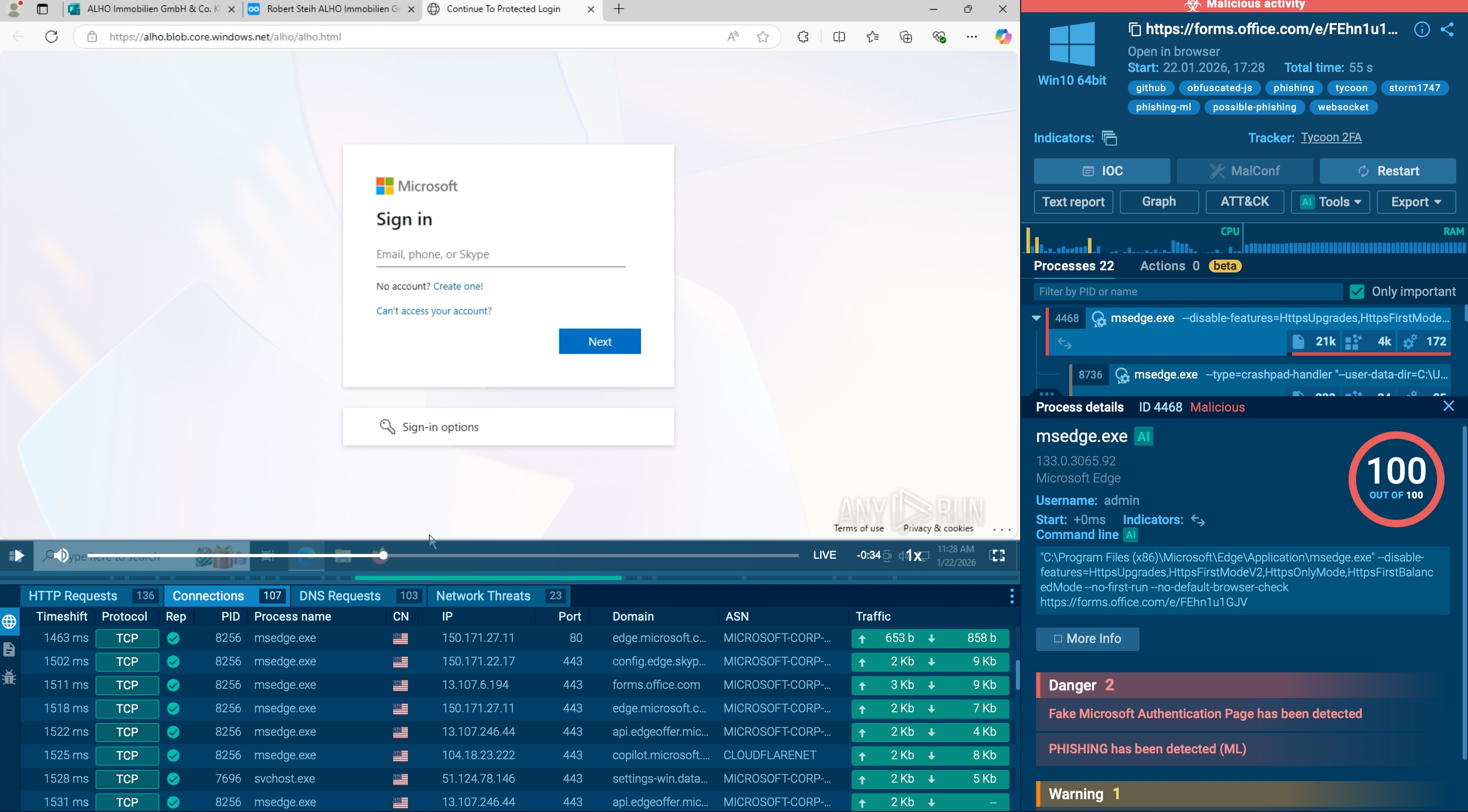
Analysts interacting with fake Microsoft login page inside ANY.RUN sandbox, revealing full attack chain in just 55 seconds
Outcomes for SOC teams:
- earlier visibility into phishing behavior before user exposure
- faster decisions based on real attack evidence
- more actionable IOCs and TTPs for downstream detection
- lower risk of missed credential theft and account compromise
Step #3: Automated Triage. Handling More Phishing Without Adding More Pressure
Phishing volume is one problem. Complex phishing flows are another. Many attacks now hide behind QR codes, CAPTCHAs, redirects, and multi-stage pages, forcing analysts to spend time clicking through steps just to reach the real malicious content.
ANY.RUN solves this by combining automation with safe interactivity. The sandbox imitates analyst behavior during execution, follows the phishing flow automatically, and reveals the full attack chain without requiring manual effort at every stage.
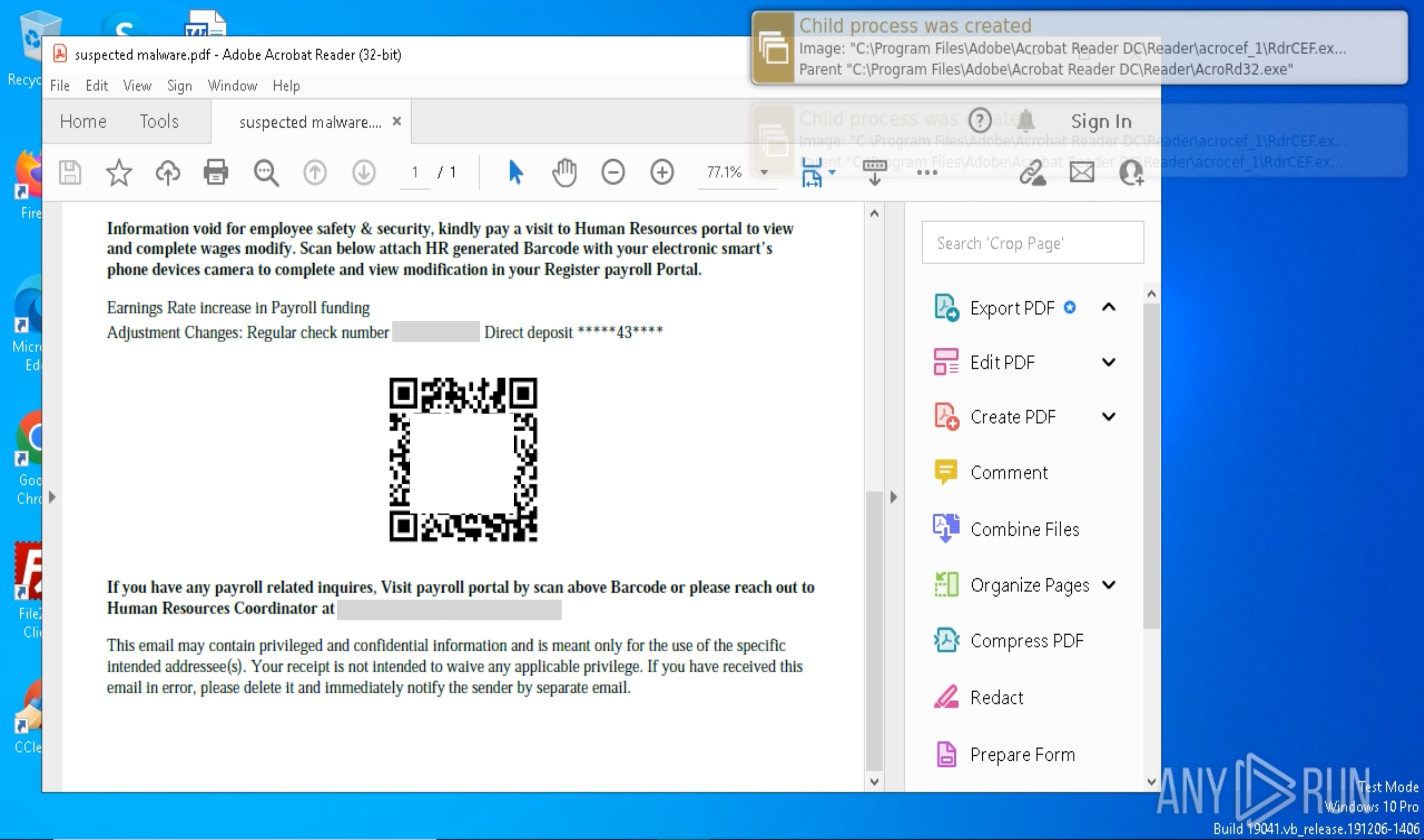
Phishing attack with a QR code analyzed inside ANY.RUN sandbox
Outcomes for SOC teams:
- more phishing cases handled without adding headcount
- less repetitive manual work for analysts
- faster confirmation of multi-stage attacks
- more reliable verdicts for evasive phishing campaigns
Strengthen Your SOC’s Ability to Stop Phishing Early
Modern phishing campaigns are designed to delay confirmation and exploit gaps in visibility. When investigation workflows rely only on surface indicators, attackers gain the time they need to capture credentials and move across business systems. Building a detection model that combines SSL decryption, interactive analysis, and automated triage helps SOC teams confirm phishing faster and reduce the window attackers have to act.
Many organizations have already adopted this approach. CISOs implementing ANY.RUN sandbox into their processes report measurable operational improvements such as:
- 3× stronger SOC efficiency, enabling teams to investigate more threats without expanding headcount
- Up to 20% lower Tier 1 workload, reducing analyst pressure and investigation backlogs
- 30% fewer Tier 1 → Tier 2 escalations, allowing senior specialists to focus on complex threats
- 21 minutes less MTTR per case, shrinking the attacker’s window to exploit stolen access
- Earlier detection and clearer response, lowering breach exposure and operational risk
- Cloud-based analysis with no hardware overhead, simplifying deployment and reducing infrastructure costs
By detecting phishing behavior earlier and confirming attacks with real evidence, security teams can move from reactive investigation to faster, more confident response.
Integrate ANY.RUN into your SOC workflows to expose hidden phishing behavior earlier, reduce investigation delays, and lower the risk of credential-driven business compromise.

