How Top SOCs Automate Detection of Evasive Phishing Attacks
Image Source: depositphotos.com
Phishing is no longer sloppy or easy to spot. Modern attacks are clean, targeted, and sold as full-service phishing kits. They mimic trusted brands, use CAPTCHAs to block scanners, and quietly steal credentials behind polished, convincing pages.
For SOC teams, this creates a serious problem. Traditional detection methods often miss these threats entirely, until the real damage is done.
But leading SOCs have found a way to fight back.
Let’s explore how they’re automating the detection of today’s most evasive phishing attacks and catching what others miss.
The Automation Gap in Phishing Detection
As phishing tactics evolve, many SOCs still rely on manual workflows, reviewing suspicious emails one by one, opening attachments, and trying to reconstruct what the attacker intended. It’s repetitive, time-consuming, and prone to human error.
But top-performing SOCs have moved beyond that.
They automate the entire detection chain, from ingesting phishing emails to triggering evasive payloads and extracting IOCs, without needing analyst input at every step.
How? By using tools that behave like real users, not static scanners.
A great example of this approach is ANY.RUN's interactive sandbox, which automates the full phishing detection flow by simulating real user havior. Instead of relying on static analysis, it actively engages with the threat, uncovering hidden payloads, revealing credential theft attempts, and exposing malicious infrastructure that traditional tools often miss.
How Automated Analysis Exposed a Real Phishing Attack in Minutes
Let’s have a look at a highly targeted, multi-stage attack, pretending to come from Hitachi’s HR department.
Check real case of phishing attack
Disguised as an urgent HR message from “Hitachi Energy,” the email asked the recipient to review a new company policy by opening a PDF attachment. The message looked legitimate, flagged as important, and even included a security reminder; the kind you’d expect in a corporate environment.
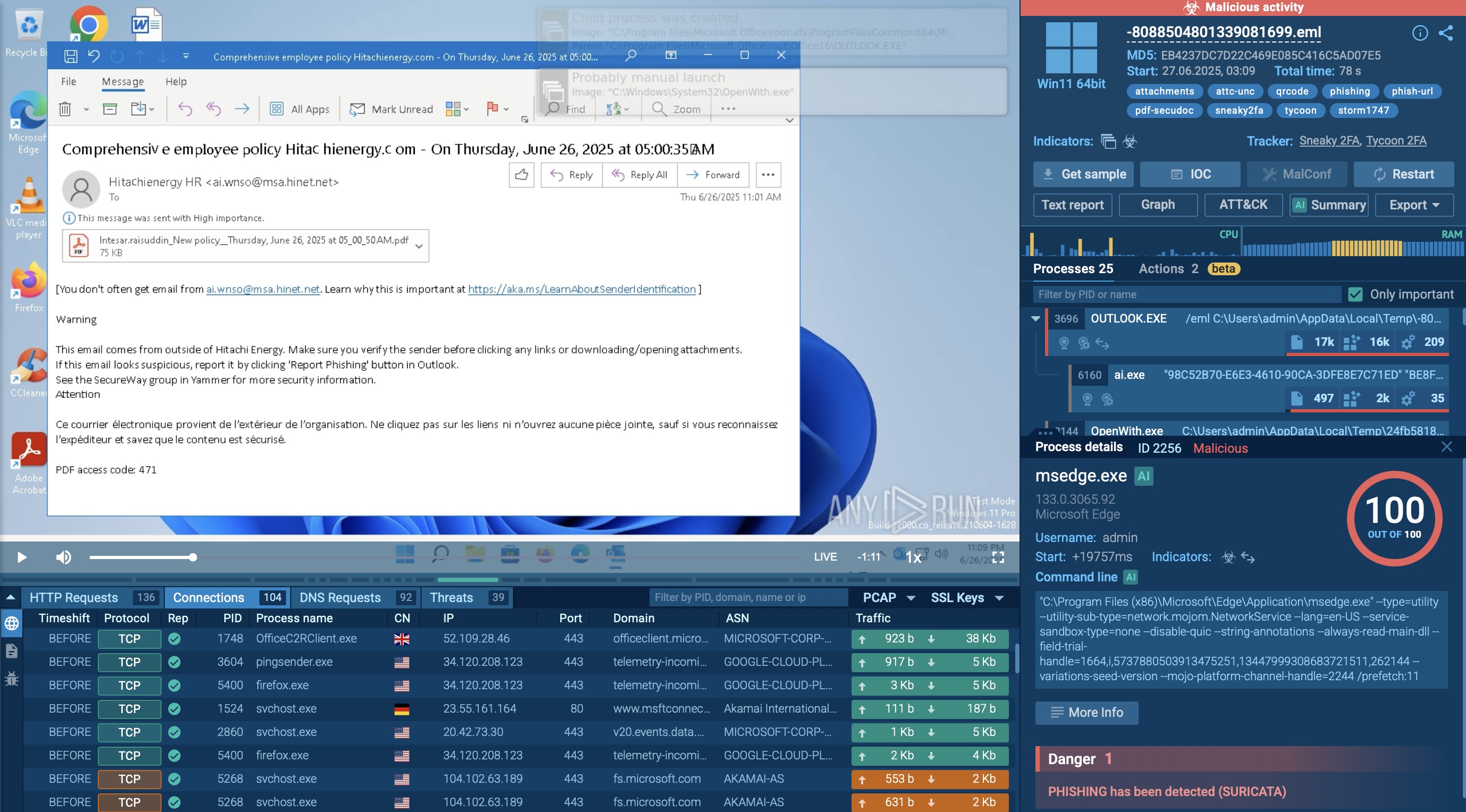
The email appears clean and trustworthy at first glance, asking employees to review a new company policy.
|
Give your SOC team the tools to detect phishing faster, reduce manual work, and boost overall response efficiency. |
Inside the PDF was no clickable link but a QR code, suggesting the policy could be accessed by scanning it with a phone.

The embedded QR code acts as the entry point to the phishing chain. It's a tactic designed to bypass traditional email security filters.
Once automated interactivity was enabled in ANY.RUN, the sandbox kicked in and took over. It scanned the QR code, extracted the hidden URL, and opened the link inside a browser, all without analyst input.
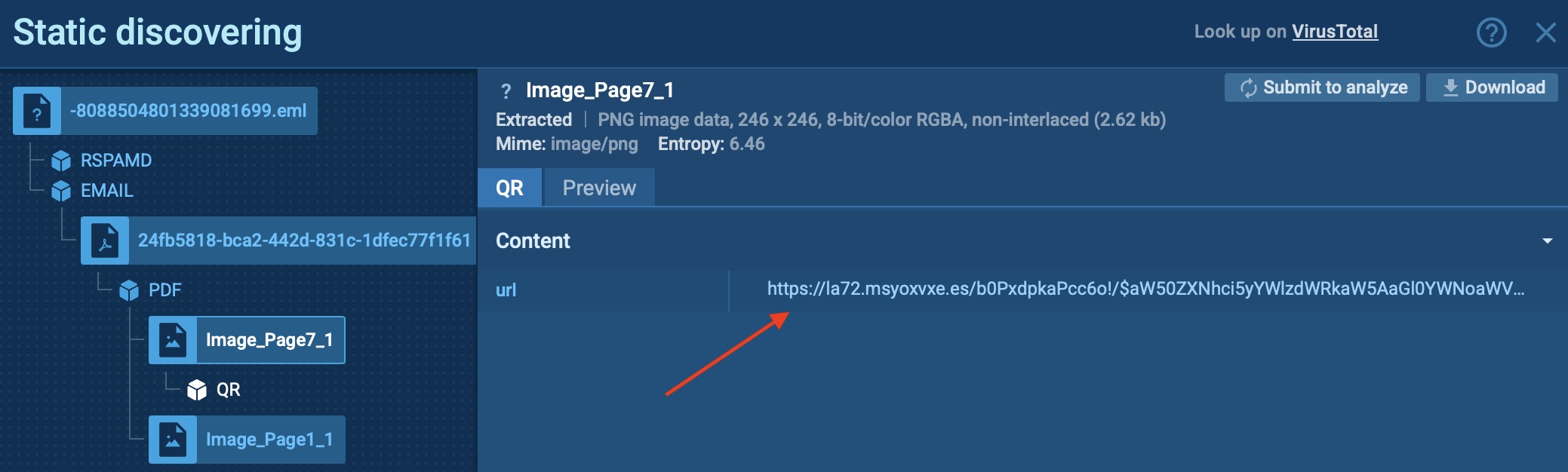
ANY.RUN automatically detects the malicious domain embedded inside the QR code, exposing the next step of the attack.
The attackers had another layer of defense: a Cloudflare CAPTCHA meant to stop automated scanners. ANY.RUN passed it, just like a human would, and reached the final destination; a fake Microsoft login page, almost indistinguishable from the real thing.
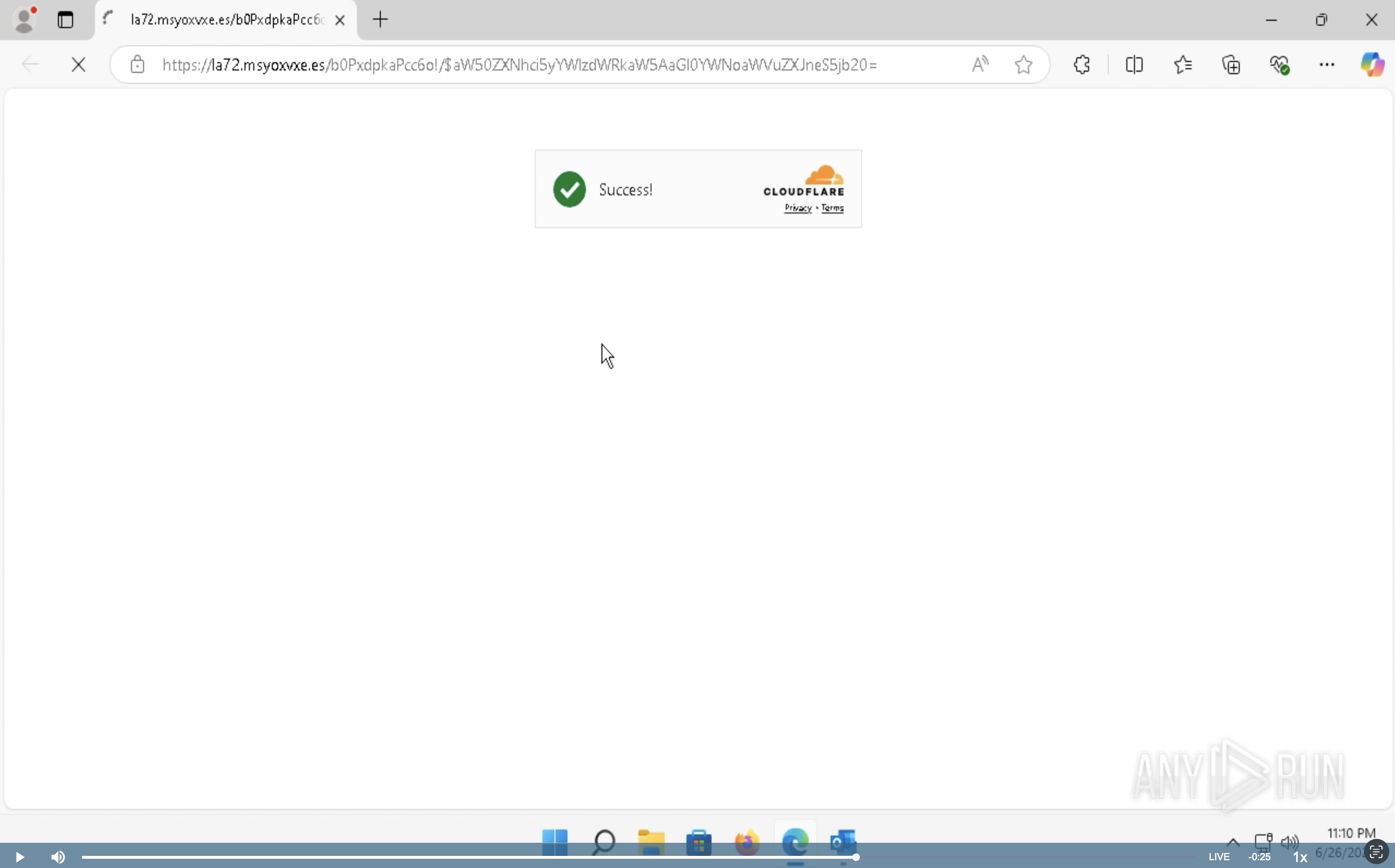
After bypassing the CAPTCHA, the sandbox reveals the fake login form, used to steal user credentials.
In just a minute, the sandbox exposed:
- The original phishing email
- The PDF with embedded QR code
- The malicious URL and redirection chain
- CAPTCHA protection
- A credential harvesting page
- And the full chain of behavior, processes, TTPs, and IOCs; all mapped and ready for export
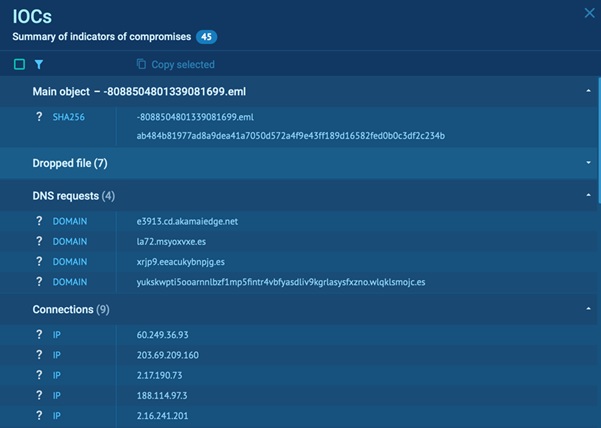
Gathered IOCs of phishing attack for easy and fast access
All of this happened automatically, without a single click from the analyst.
The SOC Advantages of Automated Phishing Analysis
Attacks like this are designed to slip through cracks, hiding behind QR codes, CAPTCHAs, and realistic branding. But with ANY.RUN’s automated interactivity, your SOC detects these threats faster and sees them fully unfold.
- Faster results: Get from suspicious email to a clear verdict in minutes
- No need for manual clicking: The sandbox does the heavy lifting: opens files, follows links, solves CAPTCHAs, and surfaces the threat
- Takes pressure off junior analysts: They can handle phishing triage confidently without needing constant help
- More focus for senior staff: Experienced analysts gain time for proactive threat hunting, rule tuning, and critical investigations
- Keeps the whole team moving faster: Less back-and-forth, fewer delays, and quicker response across the board
- Works with your stack: RUN integrates easily into existing SOC workflows via API and SDK, no need for extra tools or context-switching
- Better overall performance: Teams using ANY.RUN report up to 3x faster analysis and response across phishing investigations
Boost Your Team’s Impact with Automated Phishing Detection
For SOC leaders, automation is about results that scale.
With ANY.RUN handling phishing analysis end-to-end, teams spend less time chasing individual alerts and more time improving their overall detection and response strategy. The impact includes lower mean time to respond (MTTR), fewer escalations, and faster containment, even during high-volume incidents.
You also get clearer visibility across phishing campaigns. Behavioral patterns, IOCs, and tactics are all mapped and exportable, making it easier to improve rules, train staff, and brief stakeholders.
With automated phishing detection in place, your team can respond faster, reduce pressure across all roles, and improve overall SOC performance without scaling headcount.
Start your 14-day trial and experience how ANY.RUN helps your team detect and respond to phishing threats faster, with less manual effort and better visibility.

