ipMonitor Free Edition: Essential IT Monitoring
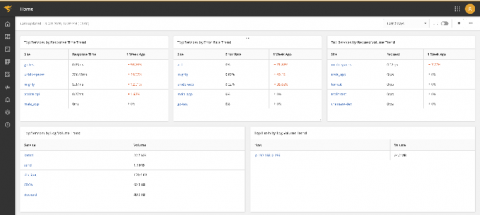
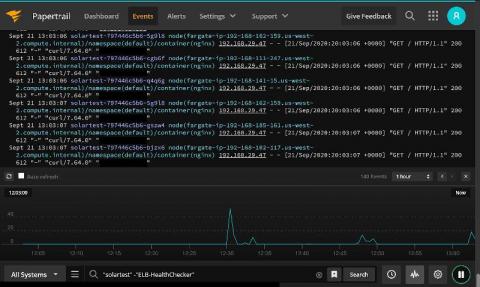
SolarWinds® ipMonitor® is built to be quick, affordable, and agentless monitoring software for your network, servers, and applications. ipMonitor delivers out-of-the-box visibility into essential availability and performance metrics for your critical IT environment, and includes a built-in database and web server, so you don’t need to install anything but ipMonitor.