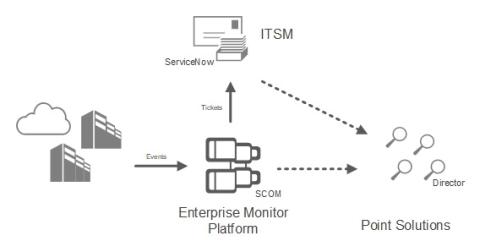
Why monitor Citrix with SCOM, if you have Citrix Director?
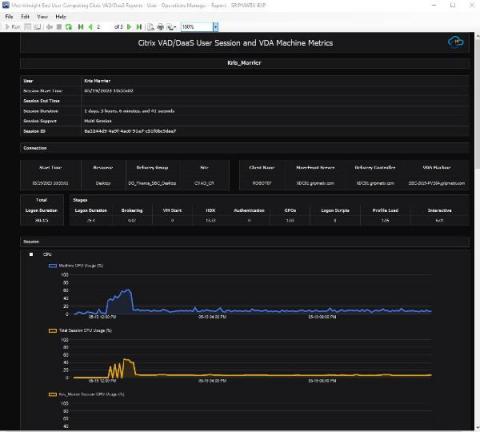
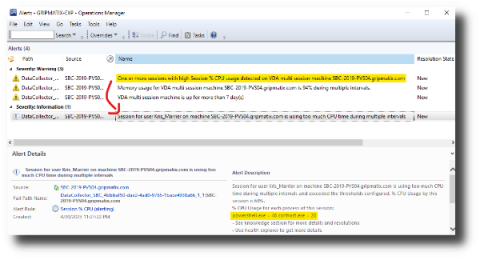
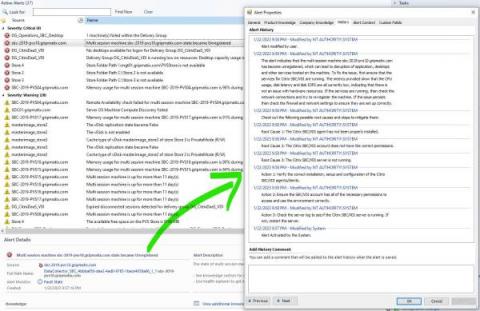
In the dynamic field of IT infrastructure monitoring, particularly for Citrix VAD and DaaS, the combination of SCOM and specialized point solutions like Citrix Director (CVAD) and Monitor (DaaS) represents a powerful, synergistic approach.