Operations | Monitoring | ITSM | DevOps | Cloud
The New Model for Network Security: Zero Trust
The old security model, which followed the “trust but verify” method, is broken. That model granted excessive implicit trust that attackers abused, putting the organization at risk from malicious internal actors and allowing unauthorized outsiders wide-reaching access once inside. The new model, Zero Trust networking, presents an approach where the default posture is to deny access.
Mitigating the Risks of Instance Metadata in AWS EKS
Compromising a pod in a Kubernetes cluster can have disastrous consequences on resources in an AWS Elastic Kubernetes Service (EKS) account if access to the Instance Metadata service is not explicitly blocked. The Instance Metadata service is an AWS API listening on a link-local IP address. Only accessible from EC2 instances, it enables the retrieval of metadata that is used to configure or manage an instance.
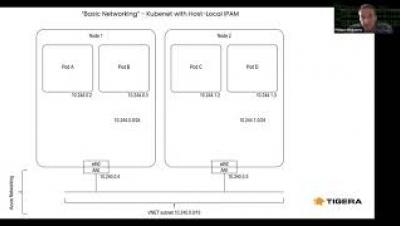
Getting up and running with Calico on AKS
Visibility and Troubleshooting Modern Applications with Calico Enterprise and OpenShift
How to Secure and Troubleshoot your Microservices Network on Amazon EKS
Security Policy Self-Service for Developers and DevOps Teams
In today’s economy, digital assets (applications, data, and processes) determine business success. Cloud-native applications are designed to iterate rapidly, creating rapid time-to-value for businesses. Organizations that are able to rapidly build and deploy their applications have significant competitive advantage.