CISOs, This Is How You Prevent Phishing Incidents in 2026
Image Source: depositphotos.com
By 2026, phishing has evolved in terms of methods in use and the scope of attacks to the point where static tools and email filters are no longer sustainable. In these conditions, the prevalence of manual malware analysis in security teams becomes an issue in itself.
In businesses and organizations, the alert volume is too high to rely on manual investigation. It slows response times, overwhelms analysts, and lowers focus on high-priority tasks.
The benefits in speed and efficiency of an automated workflow compared to manual are too impressive to ignore. Learn how to establish an enhanced SOC with sustainable protection against phishing, powered by strong enterprise-grade solutions.
Why Traditional Anti-Phishing Workflows Are No Longer Enough
- Manual triage slows down phishing response
The usual analysts’ routine in many SOCs is made of a long chain of manual steps, from opening attachments in isolated VMs to capturing the findings. Each step might not be that time-consuming on its own, but when phishing campaigns occur at large scale, any delay is high-risk.
Manual processing, complicated by multi-stage attacks, hidden scripts, and slow payload execution put the entire infrastructure at risk. Delayed response and missed alerts are common signs of an under-optimized workflow.
- Resource-draining indicator collection
The extraction of indicators of compromise (IOCs) from phishing attacks is another potentially tedious process for analysts. It requires more that retrieval, but also also cross-checking against different resources and reputation or threat intelligence portals.
This not only slows down the operations but also lowers analysts’ ability to focus, contributing to burnout, fatigue, and error-prone decisions.
- Reporting becomes a hidden issue
The investigation doesn’t end with detection: an often-overlooked part of the task is to document your findings. This is key for the justification of decisions and presentation of results.
But for analysts, this adds another layer of friction. Capturing screenshots, URLs, IOCs, and other data in another comprehensive report is another factor impacting SOC capacity.
What a Modern Phishing Analysis Workflow Looks Like
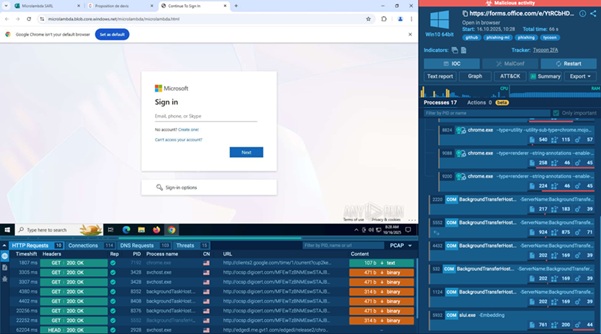
ANY.RUN sandbox analysis in action
Equipping your SOC team with purpose-built sandboxing solutions is a major way to contribute to better phishing prevention. From initial triage to conclusive reporting, a sandbox facilitates each stage of investigation.
Instant threat detonation for phishing threats
Analysts can upload a suspicious email or attachment, and the sandbox will detonate it instantly inside a fully controlled VM. Within 20-40 seconds, the sandbox reveals:
- threat behavior
- network connections and redirects
- script execution
- dropped files and evasion techniques
An interactive sandbox offers immediate detonation in a controlled VM that doesn’t require complex setup and maintenance costs. By accessing a cloud-based, always ready for work environment uncover malicious behavior in under a minute.
ANY.RUN’s Interactive Sandbox offers full visibility into attacks. It’s more than a virtual machine — it tracks, records, and interprets every activity. Built to reveal malware configurations, unveil what’s hidden, and break down even highly evasive threats, it streamlines the workflow while leaving the analyst in control.
Strengthen your phishing defense with ANY.RUN
Prevent incidents with 3x efficiency
Automated context enrichment
Sandboxing delivers indicators to your system as soon as they emerge. They make phishing campaigns visible via
- domains
- IPs
- file hashes
- registry changes
- dropped files
Instead of hunting for context across tools and resources, get verdict, threat name, family, phishing kit, and other context in a single environment of ANY.RUN sandbox. Get full-on threat coverage without an increased load on analysts.
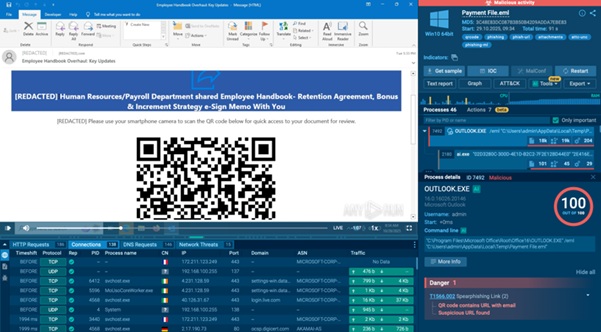
QR code-based phishing threat detonated inside ANY.RUN sandbox
Finalizing results without manual effort
ANY.RUN sandbox automatically provides a complete report for every analysis, featuring data like:
- screenshots
- network activity
- process events
- Indicators
- threat labels
Analysts can share it immediately for the case to move forward with zero manual input. ANY.RUN delivers complete, extensive reports in seconds, accelerating the entire process.
Measurable Results of Sandbox-Driven Workflow
Organizations that adopt interactive sandboxing by ANY.RUN gain:
- Up to 90% of malicious activity exposure within the first 60 seconds of detonation
- Faster triage, as reported by 94% SOC teams
- 3× boost in investigation throughput
- A drop in false-positive rates
- Up to a 58% increase in threats identified overall
These outcomes add up for SOC teams to grow in speed capacity, enabling better proactive and reactive defense of their infrastructure.
Conclusion
In 2026, phishing prevention is no longer only about detection but also about operational efficiency. CISOs who invest in sandboxing-driven workflows empower analysis for faster response, reduce their workload, and prevent phishing incidents with more impact and scalability.

