Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
Deploying a Containerized App in Google GKE
Because of its popularity and widespread adoption, Kubernetes has become the industry’s de facto for deploying a containerized app. Google Kubernetes Engine (GKE) is Google Cloud Products’ (GCP) managed Kubernetes service. It provides out-of-the-box features such as auto-scaling nodes, high-availability clusters, and automatic upgrades of masters and nodes. In addition, it offers the most convenient cluster setup workflow and the best overall developer experience.
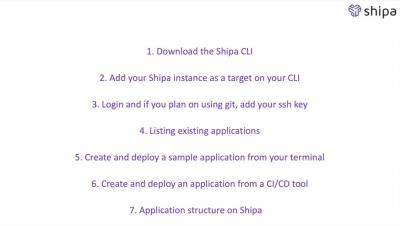
Getting started with Shipa
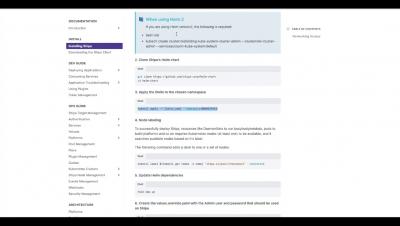
How to install Shipa
Connecting Kubernetes clusters to shipa
On-Demand Webinar: Extending Your Fortigate Next-Gen Firewall to Kubernetes
Azure you shot an ARO through our hearts... Confidently observe and secure Azure Red Hat OpenShift with Sysdig and Arctiq
It has arrived! Azure Red Hat OpenShift 4 is here and generally available; now, how do you add even more granular security and faster time to repair (MTTR) for your teams? Sysdig, that’s how!
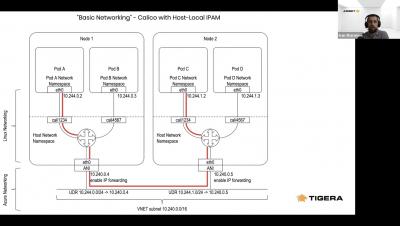
Getting up and running with Calico on AKS
Kubernetes Network Policy Introduction
Qovery and the Twelve-Factor App methodology
The Twelve-Factor App methodology is a methodology for building platform-agnostic and resilient applications. It was introduced by Adam Wiggins while working at Heroku in 2011. Nearly 10 years later, this methodology is still considered by the developer community as an excellent practice to follow when building an application. In this article, we will see step by step how Qovery respects and improves the 12-factor methodology. Here we go.