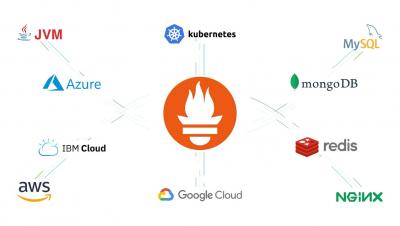
No pain... More gain! Sysdig Monitor radically simplifies monitoring integrations based on open source
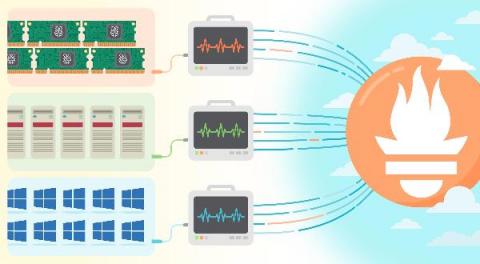
Monitoring services and applications in just a few clicks – that’s the dream of every SRE and developer, but this is very difficult because most applications don’t expose metrics in a standardized format. This article will introduce the current pros and cons of the Prometheus exporters ecosystem and how we leveraged the power of the open-source exporters in Sysdig to radically simplify the user experience to allow you to monitor your applications in just a few clicks.